Iron Lock Ransomware
Protecting devices from malware has never been more critical. Modern ransomware campaigns are no longer crude experiments; many are engineered to silently infiltrate systems, cripple access to data, and pressure victims into costly decisions. Understanding how these threats operate, and how to defend against them, is a foundational step in reducing risk.
Table of Contents
Iron Lock Ransomware: A New Name in a Familiar Threat Landscape
Iron Lock Ransomware emerged during routine inspections of active malware threats by information security researchers. Technical analysis indicates that it is built on the Chaos ransomware family, a lineage known for straightforward but disruptive encryption routines. Once Iron Lock is executed, it immediately begins encrypting user data and altering filenames by appending four random characters as a new extension. For example, an image such as '1.png' may be transformed into '1.png.c0wm,' while a document like '2.pdf' could become '2.pdf.yabs.'
This renaming pattern not only signals that files are no longer accessible, but also helps the malware mark which data has already been processed.
The Ransom Note and What It Reveals
After encryption, Iron Lock drops a ransom note titled 'READ ME.txt.' The message informs victims that their files have been locked and asserts that recovery is impossible without purchasing a decryption tool. The demanded payment is set at approximately $1,500 in Bitcoin.
Notably, the note does not provide any contact information. This absence is unusual and suggests that Iron Lock may still be under development or being distributed without a fully operational extortion infrastructure. Regardless of intent, the impact remains serious: encrypted data is typically inaccessible without the attacker's unique decryption key.
Security professionals strongly discourage paying ransoms. There is no assurance that cybercriminals will deliver a functioning decryption tool, and payment only fuels further criminal activity. In many incidents, the most reliable path to recovery is restoring data from clean, offline backups.
Why Removal Matters Beyond the Initial Attack
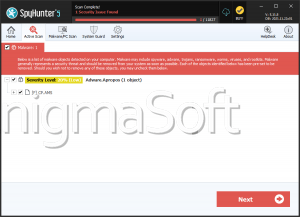
If Iron Lock remains on an infected system, it can continue encrypting newly created or restored files and may even attempt to move laterally across connected devices. This means that one compromised computer can become a gateway to broader network damage. Prompt isolation of the affected system and thorough scanning with reputable security software are essential steps to prevent additional losses.
Common Infection Pathways
Like many ransomware families, Iron Lock is designed to rely on human error and exposed systems rather than sophisticated zero-day exploits. Cybercriminals often disguise malware as legitimate files or updates to convince users to run them. Common delivery channels include phishing emails, deceptive websites, pirated software bundles, compromised advertisements, and infected removable media. Outdated software and unsecured peer-to-peer networks also remain popular vectors for ransomware distribution.
Strengthening Your Defenses: Security Practices That Make a Real Difference
Effective protection against ransomware is built on layered security and consistent habits. While no single measure is foolproof, combining multiple safeguards dramatically lowers the likelihood of a successful attack and limits damage if one occurs.
Key practices users should implement include:
- Keeping operating systems, browsers, and applications consistently updated to close known security vulnerabilities.
- Using reputable, up-to-date security software that offers real-time protection and behavioral detection.
- Maintaining regular backups stored offline or in secure cloud environments isolated from everyday system access.
- Exercising caution with email attachments, links, and downloads, especially those received unexpectedly.
- Limiting user privileges so that everyday accounts do not have unnecessary administrative rights.
Beyond these points, security is also a mindset. Verifying sources, avoiding 'too good to be true' offers, and treating unsolicited messages with skepticism can prevent the initial execution step that ransomware depends on.
Final Thoughts
Iron Lock Ransomware reflects a continuing trend: even when a threat appears technically simple or unfinished, it can still cause serious disruption. Awareness of how such malware behaves, combined with proactive security practices, remains the strongest defense. By investing time in prevention and preparedness, users and organizations alike can significantly reduce the leverage ransomware operators seek to gain.