TroxApp
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Ranking: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 4 |
| First Seen: | July 22, 2024 |
| Last Seen: | July 22, 2024 |
It is crucial for users to recognize the risks posed by Potentially Unwanted Programs (PUPs) like TroxApp, as they can compromise both the security and functionality of their devices. PUPs often enter systems unnoticed and can lead to a variety of detrimental outcomes if not promptly identified and removed.
Table of Contents
Overview of TroxApp
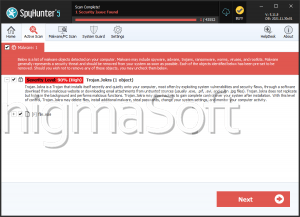
TroxApp, identified by cybersecurity researchers, is categorized as a Potentially Unwanted Program (PUP). It was discovered being distributed through a deceptive installer promoted on a scam page accessed via redirects from rogue advertising networks linked to Torrent websites.
Harmful Capabilities of PUPs
Potentially unwanted programs, including TroxApp, exhibit a range of hazardous capabilities that can negatively impact user devices and privacy.
- Adware Functionalities
One prevalent feature of PUPs is their adware-type functionalities. These programs generate revenue through intrusive advertising practices. They may display ads on various interfaces, causing disruptions and potentially leading users to click on malicious content. - Browser Hijacking
Another common capability of PUPs is browser hijacking. These programs modify browser settings such as default search engines, homepages, and new tab preferences. Users may find themselves redirected to promoted sites or encounter fake search engines that deliver unreliable or malicious content. - Data Tracking and Privacy Risks
Perhaps the most concerning functionality of PUPs is their ability to track and collect user data. This can include browsing history, search queries, cookies, usernames, passwords, and even financial information. Such sensitive data can be exploited for profit through sale to third parties, including cybercriminals.
Distribution Tactics of PUPs
Potentially Unwanted Programs like TroxApp often employ shady distribution tactics to infiltrate users' devices without their knowledge or explicit consent. These tactics typically involve:
Deceptive Installers: PUPs are often bundled with legitimate software or distributed through misleading installers that users may inadvertently download from untrustworthy sources.
Scam Pages and Rogue Advertising Networks: PUPs are promoted through scam pages that utilize rogue advertising networks. Users may be redirected to these pages while browsing or downloading files from torrent or other unregulated sites.
Misleading Advertisements: PUPs may also be disguised as useful software or updates in misleading advertisements, enticing users to click and inadvertently install them.
By understanding these distribution tactics and being vigilant while browsing and downloading software, users can significantly reduce the risk of unintentionally installing PUPs like TroxApp on their devices.
In conclusion, users must remain cautious and informed about the dangers posed by Potentially Unwanted Programs such as TroxApp. Vigilance in recognizing suspicious activities and adopting safe browsing practices is essential to maintaining the security and privacy of personal devices and data.
Registry Details
Directories
TroxApp may create the following directory or directories:
| %appdata%\Troxbox Publish |