AT&T Email Scam
Upon analyzing the 'AT&T' email, cybersecurity experts have identified it as a fraudulent message aimed at carrying out a refund scheme. This email is designed to appear as a confirmation of a service transfer to another provider.
The intent behind the email is to deceive recipients into engaging with fraudsters by suggesting that they can cancel impending charges related to the supposed transfer. Such tactics can take various forms, all posing significant risks.
It's crucial to highlight that emails like this one are entirely bogus and have no affiliation with AT&T Inc. or any legitimate companies.
Table of Contents
The AT&T Email Scam Seeks to Scare Users into Contacting the Fraudsters
The spam email, titled 'DSL Broadband Service Transfer to AT&T,' falsely claim that a service transfer request has been processed successfully. They state that starting from the next billing cycle, the recipient's home phone and Internet services will be provided by AT&T. Additionally, they mention a transfer fee of $389.00, which they claim has already been charged and will reflect in the recipient's bank statement within 48 hours. Recipients are also informed that they can cancel the transfer by calling a provided number.
However, all the information presented in the email is fraudulent and bears no relation to AT&T Inc. or any legitimate service providers.
This spam correspondence exhibits typical characteristics of a refund scheme. These tactics often utilize refund-related themes (like chargeback or cancellation) to trick individuals into contacting fake support lines. The entire fraud can unfold over the phone, with scammers attempting to extract personal information or payments from victims.
Falling for the AT&T Email Scam May Have Serious Consequences
During phone calls, fraudsters posing as customer support representatives may attempt various tactics to deceive users into revealing sensitive information, transferring money, or downloading malicious software.
Sensitive data targeted by the tactics can include login credentials for email, social media, e-commerce sites, cryptocurrency wallets and online banking. Additionally, fraudsters aim to obtain personally identifiable information such as name, age, gender, nationality, marital status, occupation, home and work addresses and contact details. They may also seek finance-related data such as banking account details and credit/debit card numbers.
Refund schemes often bear similarities to technical support schemes, where fraudsters request remote access to victims' devices. They typically use legitimate remote access software to establish a connection. Under the guise of assisting with a refund process, victims are coerced into accessing their online bank accounts.
To make tracing difficult, fraudsters frequently employ methods like cryptocurrencies, gift cards, or hiding cash in seemingly innocent packages that are shipped. These methods reduce the likelihood of fraudsters being caught and victims recovering their funds.
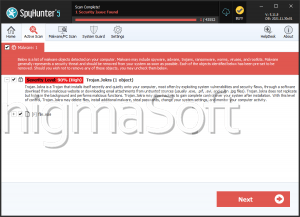
Once connected to victims' systems, cybercriminals may remove genuine security tools, install fake security software, or infect devices with malware such as Trojans, ransomware or crypto-miners.
Red Flags Indicating Fraud and Phishing Emails
Recognizing potential tactics and phishing emails is crucial for protecting oneself from cyber threats. Here are some red flags to watch out for:
- Unexpected Emails: If you get an email from a company or individual you didn't expect to hear from, especially if it asks for personal information or contains urgent requests, be cautious.
- Generic Greetings or Salutations: Phishing emails often use generic greetings like 'Dear Customer' instead of referring you by name. Legitimate companies usually personalize their emails with your name.
- Spelling and Grammatical Errors: Poor spelling, grammar mistakes, and awkward language are common signs of phishing attempts. Legitimate companies usually have professional communication standards.
- Urgent Requests or Threats: Emails that create a sense of urgency, threatening consequences if you don't act immediately, are often phishing attempts. They may affirm that your account will be suspended, or you'll face legal action if you don't comply.
- Suspicious Links: Move your mouse over any email's links (without clicking) to uncover the actual URL. Phishing emails often contain links that don't match the sender's domain or lead to suspicious websites.
- Requests for Personal Information: Legitimate companies typically don't ask you to provide private information like financial details, passwords or social security numbers via email.
- Attachments from Unknown Senders: Be wary of email attachments from unknown sources. They may contain malware or viruses. Even if the sender seems familiar, verify before opening attachments.
- Unusual Sender Addresses: Check the sender's email address carefully. Phishing emails may use slight variations of legitimate domains or completely unrelated addresses.
- Unusual Requests: Emails requesting unusual actions like sending money, wiring funds, or clicking on unfamiliar links should raise suspicion.
- Offers That Are Too Good to Be True: Emails promising unexpected rewards, lottery winnings, or extremely discounted offers are often phishing attempts aiming to lure you into providing personal information.
- Mismatched Branding: Phishing emails may use logos and branding that look slightly off or different from the official company branding.
- Emotional Manipulation: Some phishing emails may attempt to evoke emotions like fear, curiosity, or excitement to prompt you to take action without thinking.
- Emails from Unknown Contacts: Be cautious of emails from unknown contacts, especially if they contain strange attachments or links.
Remember, if you suspect an email is a scheme or phishing attempt, it's safer to ignore, delete it, or report it to your email provider. Always verify requests for personal or financial information through official channels.