CrashFix Chrome Extension
Cybersecurity researchers have uncovered an active campaign, dubbed KongTuke, that abuses a malicious Google Chrome extension posing as an ad blocker. The extension is engineered to deliberately crash the browser and manipulate victims into executing attacker-controlled commands through ClickFix-style social engineering. This latest evolution of the technique has been codenamed CrashFix and ultimately delivers a previously undocumented remote access trojan known as ModeloRAT.
KongTuke, also tracked as 404 TDS, Chaya_002, LandUpdate808, and TAG-124, operates as a traffic distribution system (TDS). It profiles victim environments and redirects selected targets to malicious payload delivery infrastructure. Access to infected hosts is then sold or transferred to other threat actors, including ransomware operators, to enable secondary-stage compromises.
Threat groups previously observed leveraging TAG-124 infrastructure include Rhysida ransomware, Interlock ransomware, and TA866 (Asylum Ambuscade). The activity has also been linked to SocGholish and D3F@ck Loader, according to an April 2025 report.
Table of Contents
From Chrome Web Store to Compromise
In the documented infection chain, victims searched online for an ad blocker and were served a malicious advertisement that redirected them to a browser extension hosted directly on the official Chrome Web Store.
The extension, named 'NexShield – Advanced Web Guardian' (ID: cpcdkmjddocikjdkbbeiaafnpdbdafmi), presented itself as an 'ultimate privacy shield' claiming to block ads, trackers, malware, and intrusive web content. Before its removal, it accumulated at least 5,000 downloads.
Technically, the extension was a near-identical clone of a legitimate ad-blocking extension. Beneath the familiar interface, however, it was designed to display a fabricated security warning stating that the browser had 'stopped abnormally' and prompting users to initiate a fake scan supposedly tied to Microsoft Edge.
Engineering a Crash to Manufacture Trust
If the user clicked to run the scan, the extension displayed instructions to open the Windows Run dialog and execute a command that had already been copied to the clipboard. As soon as this occurred, the extension intentionally launched a denial-of-service routine that created endless runtime port connections through an infinite loop, repeating the same step up to one billion times.
This resource exhaustion caused extreme memory consumption, rendering the browser slow, unresponsive, and eventually forcing a crash. The deliberate instability was not a side effect, it was the social engineering trigger.
Once installed, the extension transmitted a unique identifier to an attacker-controlled server at nexsnield[.]com, enabling victim tracking. Malicious activity was delayed for 60 minutes after installation, after which it re-executed every 10 minutes.
Before launching the DoS routine, the extension stored a timestamp in local storage. When the user force-quit and restarted the browser, a startup handler checked for this value. If present, the CrashFix pop-up appeared and then deleted the timestamp, creating the illusion that the warning was a consequence of the crash rather than its cause.
The DoS routine was only executed when three conditions were met: the victim UUID existed, the command-and-control server responded successfully, and the pop-up had been opened and closed at least once. This logic strongly suggests the operators wanted to confirm user interaction before fully activating the payload loop.
The result was a self-sustaining cycle. Every forced restart after a freeze re-triggered the fake warning. If the extension remained installed, the crash behavior resumed after ten minutes.
Obfuscation, Anti-Analysis, and Living-off-the-Land
The fake pop-up implemented several anti-analysis measures, disabling right-click context menus and blocking keyboard shortcuts typically used to access developer tools.
The CrashFix command abused the legitimate Windows utility finger.exe to retrieve and execute a secondary-stage payload from 199.217.98[.]108. KongTuke’s use of the Finger utility had previously been documented in December 2025.
The downloaded payload was a PowerShell command that fetched an additional script, which concealed its content through multiple layers of Base64 encoding and XOR operations, echoing techniques long associated with SocGholish campaigns.
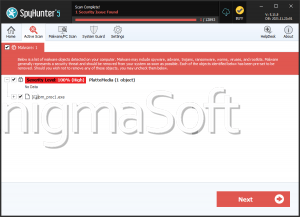
Once decrypted, the script scanned active processes for more than 50 known analysis tools and virtual machine indicators and terminated immediately if any were found. It also evaluated whether the system was domain-joined or part of a standalone workgroup, then sent an HTTP POST request back to the same server containing:
- A list of installed antivirus products
- A host classification flag: 'ABCD111' for standalone systems and 'BCDA222' for domain-joined machines
ModeloRAT: Tailored for Corporate Environments
If the infected system was identified as domain-joined, the infection chain culminated in the deployment of ModeloRAT, a Python-based Windows remote access trojan. The malware communicates over RC4-encrypted channels with command-and-control servers at 170.168.103[.]208 or 158.247.252[.]178.
ModeloRAT establishes persistence through the Windows Registry and supports the execution of binaries, DLLs, Python scripts, and PowerShell commands. It also includes built-in lifecycle controls, allowing operators to remotely update the implant or terminate it using dedicated commands.
The RAT implements a multi-tier beaconing strategy designed to evade behavioral detection:
- Under normal conditions, it beacons every 300 seconds.
- When switched into active mode by the server, it polls aggressively at a configurable interval, defaulting to 150 milliseconds.
- After six consecutive communication failures, it backs off to 900-second intervals.
- Following a single failure, it attempts reconnection after 150 seconds before returning to standard timing.
This adaptive logic allows ModeloRAT to blend into network traffic while still supporting rapid operator interaction when required.
A Two-Track Infection Strategy
While the deployment of ModeloRAT on domain-joined systems strongly indicates a focus on corporate environments and deeper network penetration, standalone machines were routed through a different multi-stage sequence. In those cases, the command-and-control server ultimately responded with the message' TEST PAYLOAD!!!!', suggesting that this parallel infection path may still be under development.
The Bigger Picture: Social Engineering by Design
KongTuke's CrashFix campaign illustrates how modern threat actors are refining social engineering into a fully engineered control loop. By impersonating a trusted open-source project, intentionally destabilizing the browser, and then presenting a counterfeit fix, the attackers transformed user frustration into compliance.
The operation demonstrates how browser extensions, trusted marketplaces, and living-off-the-land tools can be fused into a resilient infection chain, one that persists not through stealth alone, but by repeatedly manipulating the victim into triggering the attack themselves.