Trojan.Injector
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
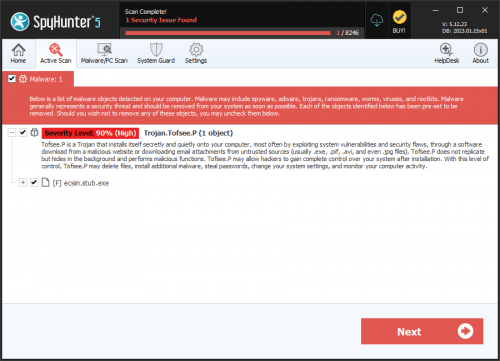
| Popularity Rank: | 3,294 |
| Threat Level: | 90 % (High) |
| Infected Computers: | 7,227 |
| First Seen: | July 24, 2009 |
| Last Seen: | April 18, 2026 |
| OS(es) Affected: | Windows |
Table of Contents
Aliases
15 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| AVG | Generic28.BQHZ |
| Fortinet | W32/Inject.EFNL!tr |
| Ikarus | Trojan-Ransom.Win32.Gimemo |
| Microsoft | Trojan:Win32/Matsnu |
| Sophos | Troj/Ransom-GV |
| AntiVir | TR/Matsnu.EB.23 |
| BitDefender | Trojan.Generic.KDV.648534 |
| Kaspersky | Trojan.Win32.Inject.efnl |
| ClamAV | Trojan.Injector-564 |
| Avast | Win32:Ransom-JW [Trj] |
| Symantec | Trojan.Ransomlock.P |
| McAfee | Generic VB.iv |
| CAT-QuickHeal | Trojan.Inject.efnl |
| AVG | Dropper.Generic4.BTME |
| Fortinet | W32/Kryptik.AL!tr |
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | file.exe | 630c537a75505c775cab7ecb4331fd7f | 2,894 |
| 2. | ohydy.exe | 97082e22d22d0233c3827aa800cd8081 | 212 |
| 3. | winmsngrn.exe | 5ed32336399cfbb32b4ae39eadbe44f4 | 37 |
| 4. | server.exe | 6a690d6ee9464b247247dc579acaf657 | 4 |
| 5. | osecilip.exe | 4d069e7d39da2a991161d4ebcfe1665b | 4 |
| 6. | csrss.exe | 48f1c9ed58b7948b33886a05c726a3aa | 3 |
| 7. | $Recycle$.exe | 8712debe5c53f26f0aa7fe272c5c9254 | 2 |
| 8. | mine.exe | 4c235cb349b71e7c181bc422162eaeba | 2 |
| 9. | winlogon.exe | 4f18ad6462c0318733f3068d5d0072b9 | 1 |
| 10. | Windows Defender.exe | d7b90f52681ebf50a75bf71b54327f80 | 1 |
| 11. | System2.exe | 0509c8e423ceca39fddb557d1d3b3195 | 0 |
| 12. | msdrive32.exe | 4fa0ebf903d127af2756a135372cb0f7 | 0 |
| 13. | abuzamnet_enc.exe | c26250804673f00acf82ffc3ec7343f9 | 0 |
| 14. | inecomm.exe | 484304e2739fb533d104654f06956312 | 0 |
| 15. | svchost32.exe | 13d994fe0816381cd863dbe9a07173a5 | 0 |
| 16. | ms87273.exe | d5445977d745c8ee312336cbb9905a68 | 0 |
| 17. | ndll.exe | 9886448ba02b730241b50906c87c97a7 | 0 |
| 18. | java.exe | 74837b73b89a529f7f4dc1eaa1859754 | 0 |
| 19. | cidrive32.exe | 2a4fc5debe6c89a772fc08d8f1bfc5de | 0 |
| 20. | sysdiag32.exe | f11719cd4d4b54ca7058f5dc80ace01f | 0 |
| 21. | jjdrive32.exe | f98711b816003449bdb6b3eb76d280e7 | 0 |
| 22. | 730.exe | 9ddb3edb042ce8fef5b96117bd4f8cfe | 0 |
| 23. | msvmcls64.exe | ca649a0b9242e7f88e4826851dc81728 | 0 |
| 24. | scvdll.exe | d8720b215ee1147b557538e9eb4208d4 | 0 |
| 25. | infocard.exe | 3b84173a87de02b6089bf5d0097fa73e | 0 |
| 26. | aca1e6.exe | 59f0d4337ee5be50b12a046822f2ef75 | 0 |
| 27. | winsvc32.exe | 7bbba0f837f7039f560a5504d99f7c9b | 0 |
Registry Details
Analysis Report
General information
| Family Name: | Trojan.Injector |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
efadae0e3b2815210f3083baee4a7dfd
SHA1:
0d5575069aa91463ba7d68a17708e6cbba5dd231
File Size:
5.68 MB, 5678030 bytes
|
|
MD5:
deff64d13688820605fe51abeb0613e5
SHA1:
4543389340df1ff3c216fe641b77d8a82cea726f
SHA256:
38AB10F979749560F479AA529445975E69A26AD9B64F07BC41D05E7C7B3F38A0
File Size:
4.72 MB, 4718538 bytes
|
|
MD5:
0314b98220bc7f874e21eb4abbfe032a
SHA1:
40952f2868e7771c9945a97022a5728754e9e477
SHA256:
0E661198B199B879C2FA30F2F99D364639B1F9E455105DE82B91B83EF1E3B465
File Size:
5.96 MB, 5958027 bytes
|
|
MD5:
5aa15b80cc50ab074302c34e7087330c
SHA1:
36f37a7fc1dfd9f92240302d9b0f8a6af521ad47
SHA256:
B934E10B7B0A0744B928D380B34908CFB5E3DC35D2284F517EDA7C6DFB8AC1FC
File Size:
5.68 MB, 5678236 bytes
|
|
MD5:
2cfd3da5537439a71f5fb6de3b8668fe
SHA1:
1350893b90506b387db3b5674a20dd31e53dfb8a
SHA256:
20959562EBCDCFCC1E4ABE5E7AA636A7964A01E2FA35FE1931AED3DF1AFEAC20
File Size:
4.75 MB, 4748603 bytes
|
Show More
|
MD5:
4abaf2e1e806bd09b8a770c143f71694
SHA1:
f6c3c4fe9a39b3e1f4c8796541027c3c3cf92b83
SHA256:
F6131485AF501832F7C1C367830130AEEEEC0CCFE20126302A0C76599BD4CD3E
File Size:
5.48 MB, 5476253 bytes
|
|
MD5:
8b3259f01428cba1806e61eb6fc810ec
SHA1:
4e93f24f2b4b16fde70fe392a5666c601d585599
SHA256:
B6151A2F1DB9F2BF2553C6C8D8C214CE83685379947D8CAEFD93E882FC999F5A
File Size:
7.09 MB, 7085522 bytes
|
|
MD5:
1243153e52887c60d14ad5ae5827118b
SHA1:
51cb808c2d4151b9f9bd259ff8c1b41e94909820
SHA256:
610BC22C5F7D66C17B0B1E97D9EC77A8F9D9905E9C3FF2B84ACCA736145E475A
File Size:
4.70 MB, 4696709 bytes
|
|
MD5:
2005b783aa53c22e2d0ca5b30a20e6d0
SHA1:
7cbebe697308a39d6e6bcb42b3a368d2b77f04dc
SHA256:
B6995DFF205F80448A0B5459314E37720D5D3FE500E58B6E6C744B39C88BBE74
File Size:
7.47 MB, 7468146 bytes
|
|
MD5:
75ae0bff32a534c29738253fdbef0176
SHA1:
436d33ce27c9544101c48cf7181609d5b4afbd09
SHA256:
BC3938E53AC27FF862BA5DB2B4F1EB9E202DD91A925884DB7661FDD3FC8F658D
File Size:
5.24 MB, 5235414 bytes
|
|
MD5:
11026338b503a7d78949c64c8b3c6617
SHA1:
a8b0b7959d17779bc7058cf99aa9ee0aa1e21a92
SHA256:
5B771657572AF8614C0B5DE180C1BD73974B369756C1834F1D864AA128EA4A46
File Size:
7.31 MB, 7312541 bytes
|
|
MD5:
65e0e7dc66ce18d77369ffec18b2b463
SHA1:
1110f4d934f23f68cfda1aad2ea4820038dda78c
SHA256:
EC2559298CFE7F5F2271C2959C39B412185CC068B84AC8D5BC4948BCBB865730
File Size:
4.78 MB, 4781056 bytes
|
|
MD5:
78434f46e7648d413825af92ef22e5c8
SHA1:
0ba3ae1800017aaa3d682b507c45b1555367fe11
SHA256:
6FE819AFAAAE9C6C25593F8C5A1259DE3932FD09D01AAD1B82A3FAF4543B9971
File Size:
2.48 MB, 2475008 bytes
|
|
MD5:
e1acee589edad429f21edebe87aaa62d
SHA1:
aebc9e2e122fce67348ff83633fe8ca6e910ecdd
SHA256:
1F36E280019E1F462624D7D1B81CD78200398C298BC05471E9B6E7912826EABF
File Size:
5.31 MB, 5314048 bytes
|
|
MD5:
20a3f23a0da4149d56bc5edabcab6050
SHA1:
1626e928ab725025fed75a4eabfde5af244ca05a
SHA256:
84C03102E7F9617F7A98A021E482D6A69CFBDD4B3B23D44BCD8A5E502DE36A12
File Size:
4.69 MB, 4686754 bytes
|
|
MD5:
3de9d06e90cee197565b0a86ef46c381
SHA1:
c775c6941a800f60c8e1bf55adf79220ddd5daeb
SHA256:
391AEABD816B18F0084851A8BCF89278E2B645BADA4263D7006136D54AA9E0FC
File Size:
741.38 KB, 741376 bytes
|
|
MD5:
6f3e4e3ebd746ec444e956f2be52015a
SHA1:
985968af9ec1c6278cc3ca1573f85d8eb960a72e
SHA256:
50F7EC5D6BC6F50B0647D95CEFED51A9BC406EF0E8E12C7DFEF2AB1326D525D2
File Size:
4.74 MB, 4736465 bytes
|
|
MD5:
aa28be6a377f128bec1811f1a39f0cd4
SHA1:
9d3e30a10bf0f114aadfe47a2f37fad28f7ff4da
SHA256:
553538A6BD9BD95F9C34F0E08717597E34EADE6557D711E3898DE4ED5491319F
File Size:
7.37 MB, 7369728 bytes
|
|
MD5:
68508fe34549e5d24401410b590862e7
SHA1:
e4bf993c3ff32b04c263a03e0a414ba44b5e4a6e
SHA256:
504DAB80E2D3B8C042859B031A12BA7B522A21DB49D2487985905E8A92450936
File Size:
5.49 MB, 5487840 bytes
|
|
MD5:
53709ea1cffb9eb6161c1c6335c07091
SHA1:
11d2b8905a133830a9beaba4b222b965908bb13f
SHA256:
C15686C3B342588A5CCE3A5B994CCBCCC78421A2DC6B4F829862BAEA402A1E4D
File Size:
6.56 MB, 6557603 bytes
|
|
MD5:
c082a1115a66836e37843e962f9270f7
SHA1:
413767112438c3d306b25aaa796c0c4cc2743773
SHA256:
4CCDABFB332F250EBAC9255BBEADCA60DE0A92F7C2070AD69780A6EB63B40824
File Size:
8.55 MB, 8552448 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have resources
- File doesn't have security information
- File has exports table
- File has TLS information
- File is 32-bit executable
- File is either console or GUI application
Show More
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Comments | This installation was built with Inno Setup. |
| Company Name |
|
| File Description |
Show More
|
| File Version |
|
| Internal Name |
|
| Legal Copyright |
|
| Original Filename |
|
| Product Name |
Show More
|
| Product Version |
|
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| AOMEI International Network Limited | Sectigo Public Code Signing Root R46 | Root Not Trusted |
File Traits
- 2+ executable sections
- dll
- HighEntropy
- imgui
- No Version Info
- ntdll
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 5,355 |
|---|---|
| Potentially Malicious Blocks: | 48 |
| Whitelisted Blocks: | 2,071 |
| Unknown Blocks: | 3,236 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Bitcoinminer.BQ
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\temp\is-14dm8.tmp\36f37a7fc1dfd9f92240302d9b0f8a6af521ad47_0005678236.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-19vho.tmp\_isetup\_setup64.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-19vho.tmp\_isetup\_shfoldr.dll | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-19vho.tmp\idp.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-19vho.tmp\innocallback.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-19vho.tmp\isdone.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-1jh23.tmp\_isetup\_setup64.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-1jh23.tmp\_isetup\_shfoldr.dll | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-1jh23.tmp\idp.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-1jh23.tmp\innocallback.dll | Generic Write,Read Attributes |
Show More
| c:\users\user\appdata\local\temp\is-1jh23.tmp\isdone.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-3jome.tmp\_isetup\_setup64.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-3jome.tmp\_isetup\_shfoldr.dll | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-3jome.tmp\idp.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-3jome.tmp\innocallback.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-3jome.tmp\isdone.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-5mh2f.tmp\_isetup\_setup64.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-5mh2f.tmp\_isetup\_shfoldr.dll | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-5mh2f.tmp\idp.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-5mh2f.tmp\innocallback.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-5mh2f.tmp\isdone.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-6th1b.tmp\436d33ce27c9544101c48cf7181609d5b4afbd09_0005235414.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-7833m.tmp\11d2b8905a133830a9beaba4b222b965908bb13f_0006557603.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-blklh.tmp\9d3e30a10bf0f114aadfe47a2f37fad28f7ff4da_0007369728.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-brdpu.tmp\0d5575069aa91463ba7d68a17708e6cbba5dd231_0005678030.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-ensj7.tmp\_isetup\_setup64.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-ensj7.tmp\_isetup\_shfoldr.dll | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-ensj7.tmp\idp.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-ensj7.tmp\innocallback.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-ensj7.tmp\isdone.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-f81vf.tmp\_isetup\_setup64.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-f81vf.tmp\_isetup\_shfoldr.dll | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-f81vf.tmp\idp.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-f81vf.tmp\innocallback.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-f81vf.tmp\isdone.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-f9e2b.tmp\_isetup\_setup64.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-f9e2b.tmp\_isetup\_shfoldr.dll | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-f9e2b.tmp\idp.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-f9e2b.tmp\innocallback.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-f9e2b.tmp\isdone.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-fpa27.tmp\a8b0b7959d17779bc7058cf99aa9ee0aa1e21a92_0007312541.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-h6f84.tmp\7cbebe697308a39d6e6bcb42b3a368d2b77f04dc_0007468146.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-hlon1.tmp\4e93f24f2b4b16fde70fe392a5666c601d585599_0007085522.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-hqev7.tmp\_isetup\_setup64.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-hqev7.tmp\_isetup\_shfoldr.dll | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-hqev7.tmp\idp.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-hqev7.tmp\innocallback.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-hqev7.tmp\isdone.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-im92f.tmp\40952f2868e7771c9945a97022a5728754e9e477_0005958027.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-kq5p0.tmp\_isetup\_setup64.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-kq5p0.tmp\_isetup\_shfoldr.dll | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-kq5p0.tmp\idp.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-kq5p0.tmp\innocallback.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-kq5p0.tmp\isdone.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-mkn18.tmp\51cb808c2d4151b9f9bd259ff8c1b41e94909820_0004696709.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-mue86.tmp\985968af9ec1c6278cc3ca1573f85d8eb960a72e_0004736465.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-njvhg.tmp\1350893b90506b387db3b5674a20dd31e53dfb8a_0004748603.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-o4l4a.tmp\_isetup\_setup64.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-o4l4a.tmp\_isetup\_shfoldr.dll | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-o4l4a.tmp\idp.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-o4l4a.tmp\innocallback.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-o4l4a.tmp\isdone.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-oeu2s.tmp\1626e928ab725025fed75a4eabfde5af244ca05a_0004686754.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-onksh.tmp\_isetup\_setup64.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-onksh.tmp\_isetup\_shfoldr.dll | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-onksh.tmp\idp.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-onksh.tmp\innocallback.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-onksh.tmp\isdone.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-op2pa.tmp\_isetup\_setup64.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-op2pa.tmp\_isetup\_shfoldr.dll | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-op2pa.tmp\idp.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-op2pa.tmp\innocallback.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-op2pa.tmp\isdone.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-qervo.tmp\_isetup\_setup64.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-qervo.tmp\_isetup\_shfoldr.dll | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-qervo.tmp\idp.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-qervo.tmp\innocallback.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-qervo.tmp\isdone.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-tk54s.tmp\4543389340df1ff3c216fe641b77d8a82cea726f_0004718538.tmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-uj14v.tmp\_isetup\_setup64.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-uj14v.tmp\_isetup\_shfoldr.dll | Generic Read,Write Data,Write Attributes,Write extended,Append data |
| c:\users\user\appdata\local\temp\is-uj14v.tmp\idp.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-uj14v.tmp\innocallback.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\is-uj14v.tmp\isdone.dll | Generic Write,Read Attributes |
Registry Modifications
Registry Modifications
This section lists registry keys and values that were created, modified and/or deleted by samples in this family. Windows Registry activity can provide valuable insight into malware functionality. Additionally, malware often creates registry values to allow itself to automatically start and indefinitely persist after an initial infection has compromised the system.| Key::Value | Data | API Name |
|---|---|---|
| HKLM\software\wow6432node\microsoft\direct3d\mostrecentapplication::name | c775c6941a800f60c8e1bf55adf79220ddd5daeb_0000741376 | RegNtPreCreateKey |
| HKLM\software\wow6432node\microsoft\directdraw\mostrecentapplication::name | c775c6941a800f60c8e1bf55adf79220ddd5daeb_0000741376 | RegNtPreCreateKey |
| HKLM\software\wow6432node\microsoft\directdraw\mostrecentapplication::id | 慂䆒 | RegNtPreCreateKey |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Process Manipulation Evasion |
|
| Process Shell Execute |
|
| User Data Access |
|
| Other Suspicious |
|
| Syscall Use |
Show More
|
| Anti Debug |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
"C:\Users\Omsqyoqq\AppData\Local\Temp\is-BRDPU.tmp\0d5575069aa91463ba7d68a17708e6cbba5dd231_0005678030.tmp" /SL5="$40062,5105057,140800,c:\users\user\downloads\0d5575069aa91463ba7d68a17708e6cbba5dd231_0005678030"
|
"C:\Users\Nriuaxzq\AppData\Local\Temp\is-TK54S.tmp\4543389340df1ff3c216fe641b77d8a82cea726f_0004718538.tmp" /SL5="$50054,4130382,140800,c:\users\user\downloads\4543389340df1ff3c216fe641b77d8a82cea726f_0004718538"
|
"C:\Users\Fgrvbwni\AppData\Local\Temp\is-IM92F.tmp\40952f2868e7771c9945a97022a5728754e9e477_0005958027.tmp" /SL5="$10280,5356402,140800,c:\users\user\downloads\40952f2868e7771c9945a97022a5728754e9e477_0005958027"
|
"C:\Users\Eqkfswiv\AppData\Local\Temp\is-14DM8.tmp\36f37a7fc1dfd9f92240302d9b0f8a6af521ad47_0005678236.tmp" /SL5="$1023E,5105107,140800,c:\users\user\downloads\36f37a7fc1dfd9f92240302d9b0f8a6af521ad47_0005678236"
|
"C:\Users\Muqdafky\AppData\Local\Temp\is-NJVHG.tmp\1350893b90506b387db3b5674a20dd31e53dfb8a_0004748603.tmp" /SL5="$300B6,4134331,140800,c:\users\user\downloads\1350893b90506b387db3b5674a20dd31e53dfb8a_0004748603"
|
Show More
"C:\Users\Kfscueur\AppData\Local\Temp\is-HLON1.tmp\4e93f24f2b4b16fde70fe392a5666c601d585599_0007085522.tmp" /SL5="$180348,6459521,140800,c:\users\user\downloads\4e93f24f2b4b16fde70fe392a5666c601d585599_0007085522"
|
"C:\Users\Vbqkrhtk\AppData\Local\Temp\is-MKN18.tmp\51cb808c2d4151b9f9bd259ff8c1b41e94909820_0004696709.tmp" /SL5="$3023C,4121198,140800,c:\users\user\downloads\51cb808c2d4151b9f9bd259ff8c1b41e94909820_0004696709"
|
"C:\Users\Unwonywh\AppData\Local\Temp\is-H6F84.tmp\7cbebe697308a39d6e6bcb42b3a368d2b77f04dc_0007468146.tmp" /SL5="$802B8,6907426,140800,c:\users\user\downloads\7cbebe697308a39d6e6bcb42b3a368d2b77f04dc_0007468146"
|
"C:\Users\Necdjatx\AppData\Local\Temp\is-6TH1B.tmp\436d33ce27c9544101c48cf7181609d5b4afbd09_0005235414.tmp" /SL5="$602BA,4660375,140800,c:\users\user\downloads\436d33ce27c9544101c48cf7181609d5b4afbd09_0005235414"
|
"C:\Users\Zqscjnub\AppData\Local\Temp\is-FPA27.tmp\a8b0b7959d17779bc7058cf99aa9ee0aa1e21a92_0007312541.tmp" /SL5="$80310,6686843,140800,c:\users\user\downloads\a8b0b7959d17779bc7058cf99aa9ee0aa1e21a92_0007312541"
|
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\0ba3ae1800017aaa3d682b507c45b1555367fe11_0002475008.,LiQMAxHB
|
"C:\Users\Hfntuxro\AppData\Local\Temp\is-OEU2S.tmp\1626e928ab725025fed75a4eabfde5af244ca05a_0004686754.tmp" /SL5="$30352,4131596,140800,c:\users\user\downloads\1626e928ab725025fed75a4eabfde5af244ca05a_0004686754"
|
"C:\Users\Nihzoxtt\AppData\Local\Temp\is-MUE86.tmp\985968af9ec1c6278cc3ca1573f85d8eb960a72e_0004736465.tmp" /SL5="$50362,4130373,140800,c:\users\user\downloads\985968af9ec1c6278cc3ca1573f85d8eb960a72e_0004736465"
|
"C:\Users\Ipefzlsx\AppData\Local\Temp\is-BLKLH.tmp\9d3e30a10bf0f114aadfe47a2f37fad28f7ff4da_0007369728.tmp" /SL5="$40326,6808795,140800,c:\users\user\downloads\9d3e30a10bf0f114aadfe47a2f37fad28f7ff4da_0007369728"
|
"C:\Users\Aokzgutw\AppData\Local\Temp\is-7833M.tmp\11d2b8905a133830a9beaba4b222b965908bb13f_0006557603.tmp" /SL5="$80308,5981959,140800,c:\users\user\downloads\11d2b8905a133830a9beaba4b222b965908bb13f_0006557603"
|