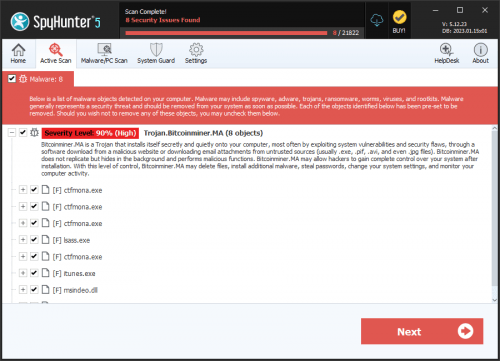
Trojan.Bitcoinminer.M
Table of Contents
Analysis Report
General information
| Family Name: | Trojan.Bitcoinminer.M |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
36b273623163ae5ace7ea0d749d3dec4
SHA1:
2f44e9209e1caecdfcecb740f9b0d5499c1b42ce
SHA256:
35F9039A6433C5E3546C9A4FFEDDC5EB883E5413D532B4D187B9BDF2A1870105
File Size:
1.47 MB, 1474048 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have resources
- File doesn't have security information
- File has exports table
- File has TLS information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
Show More
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Traits
- dll
- HighEntropy
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 1,682 |
|---|---|
| Potentially Malicious Blocks: | 328 |
| Whitelisted Blocks: | 1,166 |
| Unknown Blocks: | 188 |
Visual Map
x
x
x
x
x
x
x
x
0
x
x
x
0
x
x
x
?
x
0
?
0
?
0
?
x
0
0
?
?
?
?
?
x
0
?
?
?
?
x
?
0
0
x
?
0
?
?
x
x
x
x
x
x
0
0
0
x
x
x
x
0
0
0
x
0
?
0
?
?
?
?
x
0
x
0
x
x
x
x
x
0
0
x
?
?
?
?
x
x
x
x
x
?
?
?
?
?
x
?
?
x
0
0
0
?
0
0
0
0
0
?
x
x
0
0
x
0
0
0
?
?
?
?
?
x
x
?
?
?
?
?
?
?
?
x
?
?
?
?
x
x
0
x
x
x
?
x
x
?
x
x
x
0
0
x
x
x
x
0
0
0
0
0
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
x
?
?
?
?
?
x
?
?
?
?
?
x
x
?
x
x
x
0
x
0
0
x
x
x
x
?
?
?
?
x
0
?
?
?
0
0
0
0
0
?
?
?
x
x
x
0
0
0
0
0
?
x
?
0
?
0
?
?
0
?
0
?
0
0
0
0
0
?
?
?
?
0
?
0
?
?
?
0
0
?
0
?
x
?
0
x
x
x
?
0
x
x
?
x
?
?
x
?
x
?
?
?
?
?
x
x
?
?
?
x
x
0
0
?
?
?
0
0
x
0
?
?
?
?
0
0
0
0
0
x
0
0
0
0
x
0
0
0
0
0
0
x
x
0
x
x
0
x
x
0
x
x
0
x
x
0
x
0
x
0
x
0
0
0
x
x
x
0
0
x
x
x
?
0
x
0
x
0
0
0
x
0
x
0
0
x
x
x
x
0
0
x
x
?
?
0
x
x
0
0
x
x
0
0
0
x
x
0
0
x
x
x
?
?
0
?
x
0
x
0
?
?
0
0
x
0
x
x
x
x
0
x
0
0
?
?
?
0
0
x
x
0
x
x
x
0
?
?
x
x
x
x
x
x
x
x
x
x
?
0
0
x
?
?
x
?
?
0
0
0
0
0
0
0
x
?
x
0
x
?
0
x
0
?
0
0
0
0
x
0
0
0
0
x
x
x
x
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
x
0
0
0
x
x
x
0
0
0
x
0
0
0
x
0
0
0
0
x
x
x
x
0
x
0
0
0
0
0
0
0
x
x
0
x
x
x
x
?
x
0
x
x
0
x
x
x
0
x
0
0
x
0
0
0
0
x
0
0
x
?
x
x
0
0
x
x
x
0
0
x
x
x
x
x
x
0
x
x
x
x
?
?
?
x
?
x
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
1
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
1
0
1
1
0
0
1
0
0
0
0
3
1
1
0
0
0
2
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
1
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
2
2
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
2
0
0
2
0
0
0
0
0
0
0
0
0
0
2
0
0
1
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
1
0
0
0
0
2
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
2
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
2
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
2
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
2
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
2
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
0
1
0
2
2
1
0
1
1
1
0
0
0
0
?
?
?
?
?
?
x
?
?
?
?
?
?
?
?
?
?
?
?
?
?
x
x
x
x
x
?
x
x
x
x
?
x
x
x
x
x
x
x
x
x
x
?
0
x
?
?
?
?
?
x
x
x
x
x
x
x
?
?
?
?
?
?
?
0
0
x
0
x
?
0
x
0
0
?
0
x
?
x
x
0
?
?
0
0
x
0
?
x
x
x
x
x
x
0
0
0
0
0
?
?
?
?
?
?
0
0
?
0
x
0
0
0
x
x
x
0
x
0
0
0 - Probable Safe Block
? - Unknown Block
x - Potentially Malicious Block
? - Unknown Block
x - Potentially Malicious Block
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|
| Process Manipulation Evasion |
|
| Process Shell Execute |
|
| Anti Debug |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\2f44e9209e1caecdfcecb740f9b0d5499c1b42ce_0001474048.,LiQMAxHB
|