Solana Seeker Website Scam
In today's hyperconnected world, exercising caution while browsing the internet is not optional, it is essential. Cybercriminals continuously refine their methods, creating deceptive websites and campaigns that closely mimic legitimate platforms. A single careless click can expose sensitive data or, in the case of cryptocurrency, lead to irreversible financial loss. The recently confirmed Solana Seeker website scam is a clear example of how convincing and dangerous modern crypto fraud has become.
Unmasking the Fake 'Solana Seeker' Website
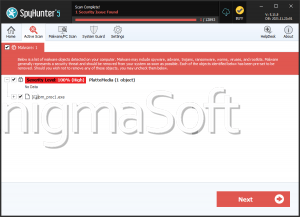
During an in-depth investigation, cybersecurity researchers identified a fraudulent website impersonating the Solana ecosystem. The fake page, discovered on token-skr.org (and potentially other domains), presents itself as an official 'Solana Seeker' platform. In reality, it has no affiliation with Solana Seeker, Solana Mobile, Solana Labs, or Solana.
The scam site closely imitates the design and layout of Solana Mobile's legitimate website (solanamobile.com), making it difficult for unsuspecting users to distinguish between the real service and the counterfeit one. By leveraging a trusted brand identity, the operators increase the likelihood that visitors will lower their guard.
The Deceptive Promise of Free SKR Tokens
The fraudulent webpage claims that visitors can receive free SKR tokens, allegedly linked to the Solana Seeker ecosystem and Solana Mobile's Web3 smartphone initiative. This so-called giveaway is entirely fake and is designed to exploit curiosity, excitement, and fear of missing out.
Such 'free token' offers are a classic social engineering tactic. By presenting a reward with no apparent risk, scammers encourage users to proceed quickly, often without verifying the authenticity of the site.
How the Crypto Drainer Steals Digital Assets
Once a user connects a cryptocurrency wallet to the deceptive website, a malicious smart contract is triggered. This contract silently authorizes a cryptocurrency drainer, a mechanism engineered to siphon assets from the exposed wallet.
These drainers can automate outgoing transactions and make them appear routine, allowing theft to continue unnoticed. More advanced variants can even evaluate the contents of a wallet and prioritize higher-value assets. By the time victims realize what has happened, their funds are often already gone.
Why Victims Cannot Recover Stolen Crypto
One of the most dangerous aspects of this scam is the irreversibility of blockchain transactions. Unlike traditional banking systems, cryptocurrency networks generally offer no central authority capable of reversing transfers.
As a result, funds stolen through the fake Solana Seeker website cannot be retrieved. This permanence is precisely what makes crypto-based scams so devastating and attractive to criminals.
Why the Crypto Sector Attracts So Many Scams
The cryptocurrency ecosystem is a preferred hunting ground for cybercriminals for several reasons. Transactions are irreversible, many platforms operate across borders, and wallet addresses are not directly tied to real-world identities. Additionally, the rapid growth of Web3 technologies means many users are still learning how wallets, smart contracts, and decentralized applications work.
This knowledge gap creates ideal conditions for deception. Scammers exploit hype around new tokens, emerging projects, and innovative devices, knowing that excitement often overrides skepticism. The promise of fast profits or exclusive access makes crypto users especially vulnerable to fraudulent schemes.
Common Techniques Used to Spread Crypto Scams
Campaigns like the fake Solana Seeker site rarely exist in isolation. They are typically promoted through a broad network of deceptive channels, including:
- Intrusive advertisements and malicious pop-ups
- Spam emails, SMS messages, and robocalls
- Browser notifications and rogue ad networks
- Typosquatted or misspelled domain names
- Social media posts and direct messages
Some of the most convincing promotions originate from hijacked or fake accounts posing as real projects, companies, influencers, or public figures. In other cases, legitimate websites compromised by attackers unknowingly host malicious pop-ups capable of launching draining scripts.
Beyond Drainers: Other Common Crypto Scam Methods
While crypto drainers are particularly dangerous, they are only one of many techniques used in this sector. Other prevalent scams involve phishing pages designed to harvest wallet credentials or direct manipulation tactics that pressure victims into manually transferring funds to attacker-controlled wallets.
These methods frequently coexist within the same campaign, increasing the probability that at least one approach will succeed.
Final Thoughts: Awareness as the First Line of Defense
The fake Solana Seeker website demonstrates how professionally crafted and convincing modern crypto scams have become. Visual authenticity, believable branding, and technical sophistication allow these schemes to bypass superficial scrutiny.
For this reason, security professionals strongly emphasize verifying URLs, avoiding unsolicited offers, and treating 'free token' promotions with extreme skepticism. In the crypto world, caution is not merely advisable, it is the primary safeguard against irreversible loss.