ShadowLock Ransomware
Protecting digital devices from malware is no longer optional but a fundamental requirement in today's threat landscape. Ransomware, in particular, continues to evolve in both technique and impact, placing personal data and business-critical information at serious risk. ShadowLock Ransomware is a clear example of how even relatively small-scale campaigns can cause severe disruption and irreversible data loss if users are not adequately prepared.
Table of Contents
ShadowLock Ransomware Overview
ShadowLock is a ransomware threat designed to deny victims access to their files through aggressive encryption. Once active on a system, it targets user data and alters filenames by appending the '.LOCKEDxX' extension. Unlike many ransomware strains that encrypt files only once, ShadowLock repeatedly encrypts the same files, stacking the extension multiple times. As a result, a file such as '1.png' may be transformed into '1.png.LOCKEDxX' and then further modified to '1.png.LOCKEDxX.LOCKEDxX,' compounding file damage and complicating recovery attempts.
Encryption Behavior and File Impact
The repeated encryption routine employed by ShadowLock significantly worsens the impact of the attack. Each encryption cycle further corrupts the original data structure, making decryption even less feasible without the original cryptographic keys. This approach increases pressure on victims by rapidly rendering files unusable and reinforcing the perception that recovery is impossible without compliance.
Ransom Note Characteristics and Demands
ShadowLock displays its ransom message as a full-screen image, reinforcing the illusion that the entire system has been locked. The note claims that all files have been encrypted and demands a payment of 0.00554 Bitcoin within a 72-hour deadline. Victims are warned that failure to comply will result in permanent data loss. The message also falsely asserts that recovery options such as Safe Mode and Task Manager are disabled, further discouraging victims from attempting self-remediation.
A notable red flag is the complete absence of contact or communication details in the ransom note. There is no email address, messaging platform, or support channel provided. This strongly suggests either a poorly constructed ransomware operation or a scam-like campaign, as victims have no way to verify payment instructions, negotiate, or confirm that a decryption tool even exists.
Risks of Paying the Ransom
Paying the demanded ransom is strongly discouraged. There is no guarantee that the attackers will provide a functional decryption tool, especially given the lack of communication options. In many cases, victims who pay receive nothing in return. Additionally, funding such operations encourages further criminal activity and may mark the victim as a future target.
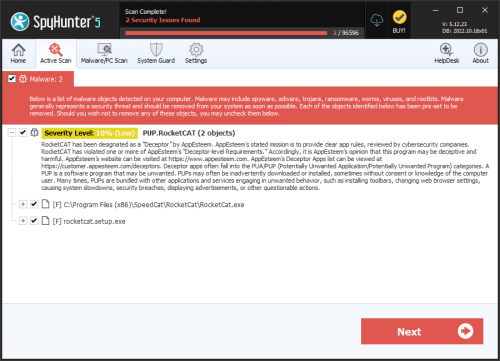
Data recovery without the attackers' tools is rarely possible unless reliable backups are available. Equally important is the complete removal of the ransomware from the infected system. Leaving ShadowLock active may result in repeated encryptions or allow the malware to spread to other devices connected to the same network.
Common Distribution Methods
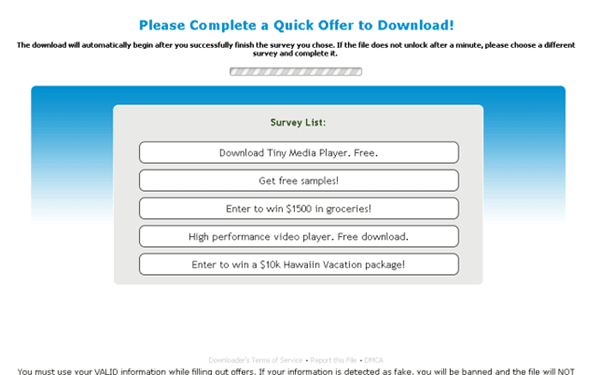
ShadowLock is typically delivered through social engineering and deceptive delivery channels that trick users into executing malicious files. These files may appear as legitimate executables, documents, scripts, ISO images, or compressed archives. Infections are often linked to unsafe or compromised websites, fake technical support pages, and misleading emails that pressure recipients into opening attachments or clicking harmful links.
Additional distribution vectors include malicious advertising, infected USB storage devices, peer-to-peer file-sharing platforms, third-party downloaders, pirated software, key generators, cracking tools, and exploitation of unpatched software vulnerabilities.
Best Security Practices to Reduce Ransomware Risk
Strengthening defenses against threats like ShadowLock requires a layered and proactive security approach. Users should maintain regular, offline backups of important data to ensure recovery options remain available even after encryption. Operating systems, applications, and firmware should be kept fully updated to close known security gaps that ransomware often exploits. Reputable security software should be installed and actively maintained, providing real-time protection against malicious files and behaviors.
Equally critical is user awareness. Email attachments and links should be treated with caution, especially when messages create urgency or come from unknown senders. Software should only be downloaded from trusted and official sources, and pirated programs or cracking tools should be avoided entirely. Disabling unnecessary macros, limiting user privileges, and monitoring unusual system behavior can further reduce the likelihood of successful infection.