Risen Ransomware
In today's digital age, protecting devices from malware threats is crucial. Malware, such as ransomware, can have devastating effects on both individuals and organizations, leading to significant data loss, financial damage, and operational disruption. One of the newest threats in this realm is the Risen Ransomware, a threatening software that encrypts users' files and demands the payment of a ransom for their recovery. Understanding how the Risen Ransomware operates and how to safeguard against such threats is essential for maintaining cybersecurity.
Table of Contents
An Overview of the Risen Ransomware
The Risen Ransomware was discovered by cybersecurity researchers who identified its unique characteristics and methods of operation. Upon infecting a system, Risen encrypts files and renames them by appending an email address and a user ID to their extensions. For instance, '1.png' is renamed to '1.png.Default@firemail.de].E86EQNTPTT', and '2.pdf' becomes '2.pdf.Default@firemail.de].E86EQNTPTT'.
Ransom Notes and Threats
The Risen Ransomware creates two ransom notes: '$Risen_Note.txt' and '$Risen_Guide.hta'. Additionally, it changes the desktop wallpaper and displays a message on the pre-login screen, ensuring the victim is aware of the breach. The ransom notes claim that the attackers have infiltrated the victim's entire network due to security flaws and have encrypted all files using a strong algorithm. They also assert that critical data, such as documents, images, engineering data, accounting information, and customer details, have been stolen.
Extortion Tactics
The ransom notes threaten that if the victims do not cooperate by an unspecified deadline, the attackers will leak or sell the gathered data. The notes state that backups have also been encrypted and are inaccessible, implying that the only way to recover files is through a specific decryption tool provided by the attackers. Victims are allowed to send up to three test files for free decryption and must use the provided email addresses, default1@tutamail.com and default@firemail.de, to contact the attackers, including their machine ID in the subject line. If there is no response within 72 hours, victims are told to contact the attackers through a provided TOR blog.
The Risks of Paying the Ransom
Despite the attackers' promises, paying the ransom is highly discouraged. There is a significant risk of being fooled, as attackers may not provide the decryption tool even after payment. Moreover, ransomware can continue to encrypt files and spread throughout the network while it remains active, causing further damage.
Security Measures to Prevent Ransomware Infections
Protecting against ransomware like Risen requires a multi-faceted approach. Here are some critical security measures users should implement:
- Regular Backups: Regularly set up a backup of important data and ensure backups are stored offline or in a secure, cloud-based solution. This ensures data recovery in case of an attack.
- Updated Software: Retain all software, including applicatons and operating systems, upgraded with the latest security patches to close vulnerabilities that ransomware can exploit.
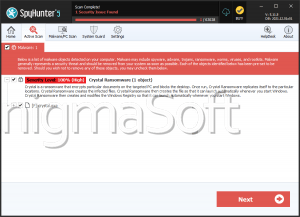
- Strong Anti-Malware: Use reputable anti-malware solutions to expose and block ransomware prior to it can cause harm. Ensure these tools are regularly updated.
- Email and Web Filtering: Implement email and web filtering solutions to block fraudulent emails and websites that may deliver ransomware payloads.
- User Training: Educate users about the dangers of ransomware and safe online practices. Emphasize the importance of not opening suspicious email attachments or clicking on unknown links.
- Network Segmentation: Segment your network to regulate the spread of ransomware. This can help contain an infection and prevent it from affecting the entire network.
- Access Controls: Implement strict access controls to restrict user permissions and block unauthorized access to sensitive data and systems.
The Risen Ransomware represents a significant threat in the landscape of cyber threats. Understanding its operation and the importance of proactive security proceeding can help mitigate the risk of infection. By implementing strong cybersecurity practices, users can protect their data and networks from the devastating impacts of ransomware.
The text on the ransom note left to the victims of the Risen Ransomware is:
'All Your Important Files Have Been Encrypted
NOTE
We have also taken your critical documents and files from different parts of your network, which we will leak or sell if there is no cooperation from your side.Our operators have been monitoring your business for a while, when we say these documents are critical, we mean it.
We await for your response before the deadline ends, After that we will continue the process of leaking or selling your documents.
We assure you that this won't happen if you cooperate with us.
CONTACT US
For more instructions, to save your files and your business, contact us by :
Email address :Default@firemail.de
didn't get any response in 24 hours ? use : default1@tutamail.comLeave subject as your machine id "-"
If you didn't get any respond within 72 hours use our Tor blog to contact us, therefore we can create another way for you to contact your cryptor as soon as possible.ATTENTION
Do not rename or change info of any file, in case of any changes in files after encryption there is a huge risk for making it unusable
Do not pay any amount of money before receiving decrypted test files
there might be many middle man services out there whom will contact us for your case and they will make a profit adding a sort of money to the fixed price
any attempts for decrypting your files through third party softwares will cause permanent damage to following files and permanent data loss
there will be a deadline until your data get sold or leaked by our team,you better corporate with us before the following deadline otherwise we will proceed to sell or leak your data without any past warnings'
The text file generated by the Risen Ransomware contains the following message from the attackers:
'RisenNote :
Read this text file carefully.
We have penetrated your whole network due some critical security issues.
We have encrypted all of your files on each host in the network within strong algorithm.
We have also Took your critical data such as docs, images, engineering data, accounting data, customers and …
And trust me, we exactly know what should we collect in case of NO corporation until the end of the deadline we WILL leak or sell your data, the only way to stop this process is successful corporation.We have monitored your Backup plans for a whileand they are completely out of access(encrypted)
The only situation for recovering your files is our decryptor, there are many middle man services out there whom will contact us for your caseand add an amount of money on the FIXED price that we gave to them, so be aware of them.
Remember, you can send Upto 3 test files for decrypting, before making payment, we highly recommend to get test files to prevent possible scams.
In order to contact us you can either use following email :
Email address : Default@firemail.de
Or If you weren't able to contact us whitin 24 hours please Email : default1@tutamail.com
Leave subject as your machine id :
If you didn't get any respond within 72 hours use our blog to contact us,
therefore we can create another way for you to contact your cryptor as soon as possible.
TOR BLOG :'