PUP.MyPC Backup
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
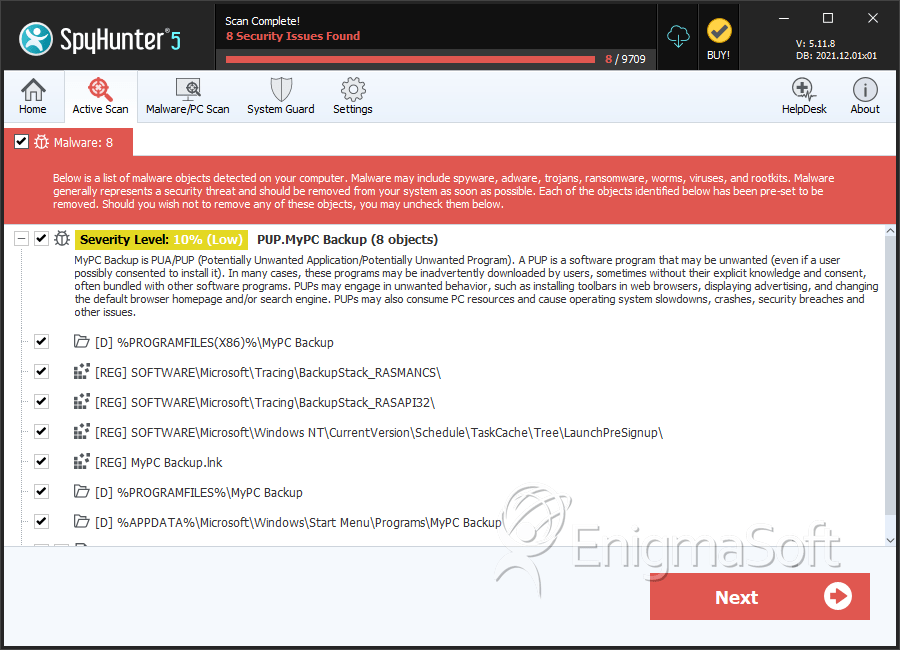
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 1,760 |
| Threat Level: | 10 % (Normal) |
| Infected Computers: | 237,197 |
| First Seen: | February 26, 2013 |
| Last Seen: | May 27, 2026 |
| OS(es) Affected: | Windows |
Table of Contents
Aliases
7 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| AVG | Generic.7D7 |
| McAfee | Artemis!4C4FD2CF29D9 |
| GData | Win32.Trojan.Agent.6QEVJE |
| Sophos | Generic PUA MH |
| McAfee-GW-Edition | Artemis |
| Avast | Win32:Malware-gen |
| Symantec | MyPCBackup |
SpyHunter Detects & Remove PUP.MyPC Backup
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | DEL_UnRegisterExtensions.exe | 32ccedc4ce079cf10c778cc75e3b40e9 | 6,715 |
| 2. | uninst.exe.vir | b3f12e4c4aafb56e945ed48d8647b563 | 4,772 |
| 3. | uninst.exe | e3f9b5981c93682c8980809fdb93f99c | 3,829 |
| 4. | BackupStack.exe | 7a67e75de5fa8680746d74761949d399 | 2,321 |
| 5. | A0044567.exe | 54d23f93cdb0aff738c75fdb6359fe51 | 1,933 |
| 6. | MyPC Backup.exe | a442aab9ad4246965be84b6b6972c426 | 1,687 |
| 7. | BackupStack.exe.vir | 3aaa70f71ba473ed9c88c83fecab28d7 | 1,552 |
| 8. | Updater.exe | 54874f3332e32e6294d9a59b4bef834b | 1,365 |
| 9. | GetText.dll | 10bb4948b3b3c1c407b2e8d0886c8723 | 900 |
| 10. | Shared Stack.dll | fa3b9eb2a835ab1fbe1ce70ab65b2213 | 873 |
| 11. | MPCBClient.dll | 5eda885eebd4c8f863df0d066d2899ec | 829 |
| 12. | UnRegisterExtensions.exe.vir | c1b78e5bb7297b4b46f16873d0073123 | 782 |
| 13. | CloudBackup2459.exe | bcba8747ab53932f8613c006444078e9 | 669 |
| 14. | A0008410.exe | a0a4dd8d711d55884c163a3784eac55e | 492 |
| 15. | MPCBContextMenu.dll | 3b6b35d7f17aeee4749581f941e73519 | 490 |
| 16. | MPCBIconOverlays.dll | cd8e6832ec6100d862ec76620f98763a | 423 |
| 17. | air5598.exe | 3d2810bd999225ac121040ba80d24494 | 378 |
| 18. | $RZNKW1Z.exe | cd5e46297de66dff69edc00499068ea8 | 278 |
| 19. | A0382240.exe | d51ce3155614d46c3be4758c7d72a8f2 | 258 |
| 20. | A0382245.exe | 69c6195f4147f69532649ac11d673be6 | 190 |
| 21. | Signup Wizard.exe | 747fbba2d1645d9a582994531577d370 | 178 |
| 22. | A0382224.exe | ce5a6ab907758186a5b5536b7ed78323 | 174 |
| 23. | debug.txt | bf8ee5a0d3582453fbe6d0c94fcdb55a | 84 |
| 24. | MyPC Backup.exe.vir | 1d913087c14071400e71a162aeb51524 | 80 |
| 25. | adv_33.exe | 3d4913e1a20168d4d3d0bc7163ba7784 | 67 |
| 26. | aff_setup.exe | 35d581e4e380ff2ba493d75120147be5 | 66 |
| 27. | DEL_MyPC Backup.exe | 1d7f9dcc554712e3239a3079c89118e0 | 56 |
| 28. | Signup Wizard.exe.vir | 76f661034f4ab0753b7981b609c6a130 | 36 |
| 29. | BackupSetup.exe | f9044bbf0bc653c378400b9b1338c52c | 1 |
Registry Details
Directories
PUP.MyPC Backup may create the following directory or directories:
| %APPDATA%\Microsoft\Windows\Start Menu\Programs\MyPC Backup |
| %PROGRAMFILES%\MyPC Backup |
| %PROGRAMFILES%\OLBPre |
| %PROGRAMFILES(X86)%\MyPC Backup |
| %PROGRAMFILES(X86)%\OLBPre |
| %TEMP%\MyPcBackup |
| %USERPROFILE%\Start Menu\Programs\MyPC Backup |
Analysis Report
General information
| Family Name: | PUP.MyPC Backup |
|---|---|
| Signature status: | Root Not Trusted |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
a8d6414a404f8029cb7f1b55b2d660ba
SHA1:
8b60d257852352eae69de2e52c226abf87a68aba
SHA256:
163BD2DF59FA0D7B71D2CA2F038D5D064A2CF4A578F3F34E9157F9FFDD69155B
File Size:
2.14 MB, 2139870 bytes
|
|
MD5:
d52c2952384187c574a7c0f338822ade
SHA1:
359b683475216cad159a593154bffa0310295906
SHA256:
7CDB204E3E600E84AA696248AB4FE05D19074097B4D751549AED38D9B6DD350A
File Size:
6.47 MB, 6473404 bytes
|
|
MD5:
38bc842f7303cdad577c5744688ef562
SHA1:
8b5ccaa060bc3178cb5d44604b0fb14a3b1aaad4
SHA256:
BADA08E36E03894D948E9667E3FF099699183BDD7A33DA792F82CC93642D5FC1
File Size:
4.80 MB, 4799348 bytes
|
|
MD5:
029527ebbd85878d8bf0bbf2a7c38877
SHA1:
75894b7f8feb6fc227b5070522ae33c14c2c08c7
SHA256:
3F7B6EEA59AAC9F1C7F6CFFEB6C0D082BF85B3B98B238CE91CFDF96D4FB829A0
File Size:
144.55 KB, 144548 bytes
|
|
MD5:
cb4461e29ef291d47fc0b9b06c297733
SHA1:
f181bb544aa1a98333d89f5feb90e1847d994e08
SHA256:
527FCDC144804C152F33CE92838F136179C377E014DB6522689FA55517D86EB2
File Size:
73.90 KB, 73896 bytes
|
Show More
|
MD5:
1488785256a8aa30fe34e88494fb69d1
SHA1:
b61aa93d03928df49689612f0aa53cb8f7f84077
SHA256:
224633433C42F77F2FC10AE00B00B3EDBF7ABAEC65433BBD36A47423D6BA8161
File Size:
8.72 MB, 8717312 bytes
|
|
MD5:
df942b42cec32c48a0527afb425add06
SHA1:
71632dc2dd94f008071402dd84ae4cb59c64c60a
SHA256:
86E2A0EBAB1077EB3A569D56995CD80B47360E54304AD172F51DF6A3220A70E0
File Size:
4.82 MB, 4818960 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Comments | Installer for Duplicate Cleaner Free. www.duplicatecleaner.com |
| Company Name | DigitalVolcano Software Ltd |
| File Description |
|
| File Version |
|
| Legal Copyright |
|
| Original Filename | TotalAV.exe |
| Product Name |
|
| Product Version |
|
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| PC Backup Software Limited | DigiCert Assured ID Root CA | Root Not Trusted |
| Digital Volcano software Ltd | UTN-USERFirst-Object | Root Not Trusted |
| SS Protect Limited | VeriSign Class 3 Public Primary Certification Authority - G5 | Root Not Trusted |
| SS Protect Ltd | VeriSign Class 3 Public Primary Certification Authority - G5 | Root Not Trusted |
File Traits
- Installer Manifest
- nosig nsis
- No Version Info
- Nullsoft Installer
- x86
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| \device\namedpipe | Generic Read,Write Attributes |
| \device\namedpipe | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\691e2668cf6045b2a8195b3c83dc3f87710079.exe | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\aff.conf | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\backupsetup.exe | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\log.txt | Read Attributes,Synchronize,Append data |
| c:\users\user\appdata\local\temp\log.txt | Read Attributes,Synchronize,Write Data |
| c:\users\user\appdata\local\temp\nsba4d7.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete |
| c:\users\user\appdata\local\temp\nsca8ce.tmp | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\nsca8ce.tmp\nsisdl.dll | Generic Write,Read Attributes |
Show More
| c:\users\user\appdata\local\temp\nsca8ce.tmp\nsisdl.dll | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\nsf2e2e.tmp | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\nsf2e2e.tmp\logex.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsf2e2e.tmp\logex.dll | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\nsf2e2e.tmp\nsisdl.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsf2e2e.tmp\nsisdl.dll | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\nsf2e2e.tmp\nsjson.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsf2e2e.tmp\nsjson.dll | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\nsf2e2e.tmp\nsrandom.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsf2e2e.tmp\nsrandom.dll | Synchronize,Write Attributes |
| c:\users\user\appdata\local\temp\nsra536.tmp\modern-header.bmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsra536.tmp\modern-wizard.bmp | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsra536.tmp\nsdialogs.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsra536.tmp\system.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nst6302.tmp\nsexec.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nst6302.tmp\nsscm.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsu2cb6.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete |
| c:\users\user\appdata\local\temp\nsxa861.tmp\langdll.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsxa861.tmp\system.dll | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\nsy60fe.tmp | Generic Read,Write Data,Write Attributes,Write extended,Append data,Delete |
| c:\users\user\appdata\local\temp\readme_6605.txt | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\settings_700.dat | Generic Write,Read Attributes |
| c:\users\user\appdata\local\temp\userguide_647.pdf | Generic Write,Read Attributes |
Registry Modifications
Registry Modifications
This section lists registry keys and values that were created, modified and/or deleted by samples in this family. Windows Registry activity can provide valuable insight into malware functionality. Additionally, malware often creates registry values to allow itself to automatically start and indefinitely persist after an initial infection has compromised the system.| Key::Value | Data | API Name |
|---|---|---|
| HKLM\system\controlset001\control\session manager::pendingfilerenameoperations | \??\C:\Windows\SystemTemp\a9dd6c3f-d641-4292-855a-e9c09c1b694b.tmp��\??\C:\Windows\SystemTemp\85968c61-a19d-4e7b-a80f-d2a1fc3c08 | RegNtPreCreateKey |
| HKLM\software\microsoft\windows nt\currentversion\notifications\data::418a073aa3bc1c75 | RegNtPreCreateKey | |
| HKLM\system\controlset001\control\session manager::pendingfilerenameoperations | *1\??\C:\Windows\SystemTemp\MicrosoftEdgeUpdate.exe.old122e4��*1\??\C:\Windows\SystemTemp\CopilotUpdate.exe.old12352��*1\??\C:\P | RegNtPreCreateKey |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Service Control |
|
| Process Shell Execute |
|
| Anti Debug |
|
| User Data Access |
|
| Network Winsock2 |
|
| Network Winsock |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
"taskkill" /f /T /IM "OLBPre.exe"
|
C:\Users\Dfrsiniu\AppData\Local\Temp\BackupSetup.exe
|
