Virus.Virut.a
O Virus.Virut.A é um vírus desagradável, que se espalha através de explorações da segurança do navegador, de IRC e de redes compartilhadas. Uma vez executado, o Virus.Virut.A se esconde profundamente na memória e tenta infectar qualquer arquivo .exe ou .scr que estiver sendo executado na sua máquina. Ele também tenta abrir um backdoor na porta TCP 65520, para que um atacante remoto possa ter acesso a qualquer informação armazenada no seu computador. Isso coloca todas as informações bancárias ou financeiras sob um grande risco, além de representar um grave risco de segurança.
Índice
Outros Nomes
7 fornecedores de segurança sinalizaram este arquivo como malicioso.
| Antivirus Vendor | Detecção |
|---|---|
| TrendMicro | TROJ_DLOADR.WHB |
| Panda | Trj/CI.A |
| McAfee | Generic Downloader.x!bbh |
| Comodo | TrojWare.Win32.Trojan.Agent.Gen |
| AVG | Generic14.ACFL |
| Avast | Win32:Trojan-gen {Other} |
| AhnLab-V3 | Win-Trojan/Downloader.77824.CV |
SpyHunter detecta e remove Virus.Virut.a
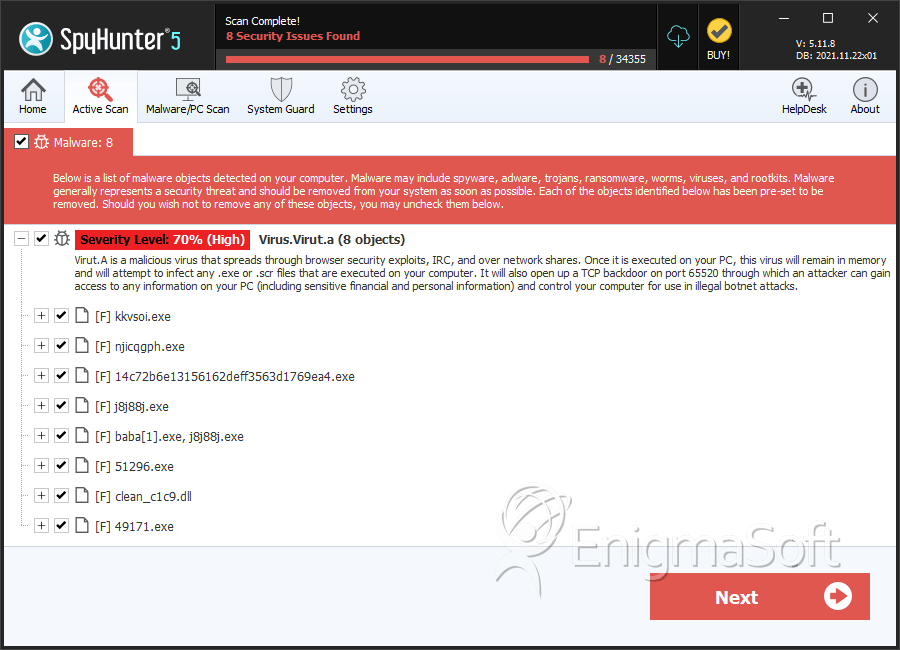
Detalhes Sobre os Arquivos do Sistema
| # | Nome do arquivo | MD5 |
Detecções
Detecções: O número de casos confirmados e suspeitos de uma determinada ameaça detectada nos computadores infectados conforme relatado pelo SpyHunter.
|
|---|---|---|---|
| 1. | kkvsoi.exe | d8959b5f68e208b0b693be67304f6046 | 0 |
| 2. | njicqgph.exe | 1c183f7e3f5d4a27084a95921cba236c | 0 |
| 3. | 14c72b6e13156162deff3563d1769ea4.exe | 14c72b6e13156162deff3563d1769ea4 | 0 |
| 4. | j8j88j.exe | b211eb32ce417bc8d685f9c9494ce777 | 0 |
| 5. | baba[1].exe, j8j88j.exe | d71ce37610732ed474cc5fc8415ae2c5 | 0 |
| 6. | 51296.exe | 5e4a95fb112dcdd9c5383012dd1b55ac | 0 |
| 7. | clean_c1c9.dll | 717e803bb4af21c000bc86e0fd781055 | 0 |
| 8. | 49171.exe | c6b0a61f184eb78a3b727447fd445396 | 0 |
| 9. | pivgrj.exe | 530e94cdf915f6b410fa7ce241474fb9 | 0 |
| 10. | 51671.exe | 31e571cda65d1bb4c74b8b59c2a6bf7e | 0 |
| 11. | giI69VPH.exe | 7ec20fa76032df5867718ace618e089f | 0 |
| 12. | xlxhgsb.exe | 6e5aedaa2c4bae55a3d19250c69ed427 | 0 |
| 13. | 60156.exe | 9937f6ad1d451ad05015762a24e0af0c | 0 |
| 14. | giI69380.exe | b6ea5ecfc21dc7b77376d80f8251b9ea | 0 |
| 15. | Resume.exe | 42c8a04c697f9f0b0520fefdb3a2c50e | 0 |
| 16. | nnabdcu.exe | 63f087b721cd76c3b04e65b1c7f80907 | 0 |
| 17. | 173906.exe | 8d27023c28fa6c0cef6729169e664ae7 | 0 |
| 18. | MailSpectre.exe | 5b7ead71abcb5e91b7d6fc15da084630 | 0 |
| 19. | logon.exe | 3241b965575268b32606cd045edf38e5 | 0 |
| 20. | epmmndvicjgn.exe | 9cc42b50ed131c60a581e3681da7bb10 | 0 |
| 21. | vivmy.exe | 1bd268b7545e403a2bc42980c036786f | 0 |
| 22. | protector.exe | 21c723c661c4b72e0ed87368c00babe7 | 0 |
| 23. | f03WtR1066.exe | 0ba4f23324781ae6209090ebabc74ca2 | 0 |
| 24. | qwgdrgusjeirkw.exe | 4111feb61a96cb261216e8e3d9665140 | 0 |
| 25. | wujein.exe | 9844bf49492e65dd7b71b2e17f93280c | 0 |
| 26. | ces005dr.exe | 410eb66fb1ab3ee3dba7ebaabcab657b | 0 |
| 27. | r1w2821.exe | b815cb04ab30ec2b85fbee51ff610dbd | 0 |
Relatório de análise
Informação geral
| Family Name: | Trojan.Virut.A |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
52707be27fe62165da492e774638129c
SHA1:
32923a93b1b813684a8cb6b141cec7b9ac59707c
SHA256:
C76508A21C1E6EDFF0FB34659FA9E640348DC474F4C20865018F74A1E11588F8
Tamanho do Arquivo:
8.59 KB, 8591 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have resources
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Traits
- 2+ executable sections
- No Version Info
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 40 |
|---|---|
| Potentially Malicious Blocks: | 35 |
| Whitelisted Blocks: | 5 |
| Unknown Blocks: | 0 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Madang.A
- Trojan.Virut.A