Pig865qq Ransomware
Security experts have recently discovered a new ransomware threat known as Pig865qq. This threateni
Security experts have recently discovered a new ransomware threat known as Pig865qq. This threatening software encrypts files on the infected system and appends the file extension '.Pig865qq' to them. Alongside this file modification, Pig865qq presents victims with a ransom note through an executable file named 'HOW TO BACK YOUR FILES.exe.'
To illustrate the impact of Pig865qq on the filenames, it transforms files such as '1.jpg' into '1.jpg.Pig865qq' and '2.png' into '2.png.Pig865qq.' This naming convention persists across various file types affected by the ransomware.
It's worth noting that Pig865qq is considered a variant within the Globe Imposter Ransomware family, indicating a possible connection to a broader network of malicious activities.
The Pig865qq Ransomware Prevents Victims from Accessing Their Data
The ransom note serves as a communication from the attackers, explicitly notifying the victim about the encryption of their files and presenting detailed instructions for decryption. To initiate the recovery process, the victim is instructed to reach out to the specified email address, china.helper@aol.com. The note specifically requests the submission of one encrypted test image, text file, or document, along with the victim's personal ID.
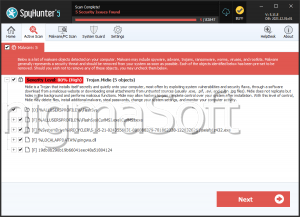
Highlighting the exclusive nature of their decryption services, the note strongly advises against seeking assistance from any other services to avoid potential fraud. Additionally, it warns against the use of antivirus programs, as they may inadvertently delete the crucial document, impeding any future communication with the attackers.
The note discourages attempts at self-decrypting files, citing the risk of potential data loss. It underlines the uniqueness of encryption keys for each user, asserting that decoders from other users are incompatible.
Attempting independent decryption often proves challenging, given that attackers typically possess the necessary decryption tools. This leaves victims with limited options for file recovery. However, the note emphatically advises against paying the requested ransom, because there is no guarantee that the attackers will uphold their promise to provide decryption tools. Succumbing to ransom demands only serves to reinforce criminal activities and does not ensure the restoration of files. Therefore, exploring alternative avenues for recovery is strongly recommended over complying with the ransom demand.
Make Sure to Protect Your Devices from Malware Threats
Protecting your devices and data from the constant menace of ransomware demands a holistic security strategy. To assist you in this effort, here are five impactful measures you can implement to strengthen your defenses:
- Regular Data Backups:
Regularly backing up your data is a fundamental security measure. In the event of data loss due to cyberattacks, hardware failures, or other unforeseen circumstances, having recent backups ensures that you can recover your information. Employ a reliable backup solution and schedule automated backups to safeguard your critical data.
- Strong Passwords and Multi-Factor Authentication (MFA):
Enhance your account security by using strong, unique passwords for each of your accounts. Incorporate a blend of upper and lowercase letters, numbers, and symbols. Additionally, enable Multi-Factor Authentication (MFA) whenever possible. MFA incorporates an extra layer of protection by requiring a secondary verification step, including a code sent to your mobile device, beside your password.
- Regular Software Updates and Patch Management:
Keep your operating system, applications and security software up to date. Regularly install updates and patches released by app sellers. These updates usually include security fixes that address vulnerabilities and protect your system from exploitation by malware or other cyber threats.
- Security Awareness Training:
Enlighten yourself and your team on cybersecurity best practices. Understand common phishing techniques, and avoid clicking on suspicious links or downloading attachments from unknown sources. By fostering a culture of security awareness, users can play a crucial role in preventing security breaches.
- Network Security and Firewall Protection:
Secure your network with a robust firewall and ensure that it is configured to filter both incoming and outgoing traffic. An installed firewall acts as a barrier between your computer or network and potential threats from the Internet. Additionally, think about using a Virtual Private Network (VPN) to encrypt your Internet connection, especially when accessing sensitive information on public networks.
Implementing these security measures collectively contributes to a more resilient defense against cyber threats, safeguarding your data and digital assets. Regularly reassess and update your security practices to adapt to evolving threats in the cybersecurity landscape.
The ransom note generated by the Pig865qq Ransomware is:
'Your files are encrypted!
To decrypt, follow the instructions below.
To recover data you need decrypt tool.
To get the decrypt tool you should:Send 1 crypted test image or text file or document to China.Helper@aol.com
In the letter include your personal ID (look at the beginning of this document). Send me this ID in your first email to me.
We will give you free test for decrypt few files (NOT VALUE) and assign the price for decryption all files.
After we send you instruction how to pay for decrypt tool and after payment you will receive a decrypt tool and instructions how to use it We can decrypt few files in quality the evidence that we have the decoder.MOST IMPORTANT!!!
Do not contact other services that promise to decrypt your files, this is fraud on their part! They will buy a decoder from us, and you will pay more for his services. No one, except China.Helper@aol.com, will decrypt your files.
Only China.Helper@aol.com can decrypt your files
Do not trust anyone besides China.Helper@aol.com
Antivirus programs can delete this document and you can not contact us later.
Attempts to self-decrypting files will result in the loss of your data
Decoders other users are not compatible with your data, because each user's unique encryption key'