Montiera Toolbar
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 2,637 |
| Threat Level: | 50 % (Medium) |
| Infected Computers: | 19,392 |
| First Seen: | May 28, 2012 |
| Last Seen: | May 5, 2026 |
| OS(es) Affected: | Windows |
Montiera Toolbar is a potentially unwanted program (PUP)/browser plug-in, which may access the PC without the computer user's agreement. Montiera Toolbar may change the default homepage and search service on the computer system with its own website and display non-stop pop-up advertisements throghout Web search sessions. In fact, activities of Montiera Toolbar may probably be executed for the commercial intention only because computer users may always be urged by Montiera Toolbar to visit questionable websites that may pay for its authprs for boosting their traffic. If the PC user has been diverted to such suspicious websites, he should go away from it immediately because the computer system may be affected by malware threats or other PC infections. Montiera Toolbar may invade the PC via two different tactics. Montiera Toolbar may be downloaded from its official website or it may propagate and enter the PC through packaged free software.
Table of Contents
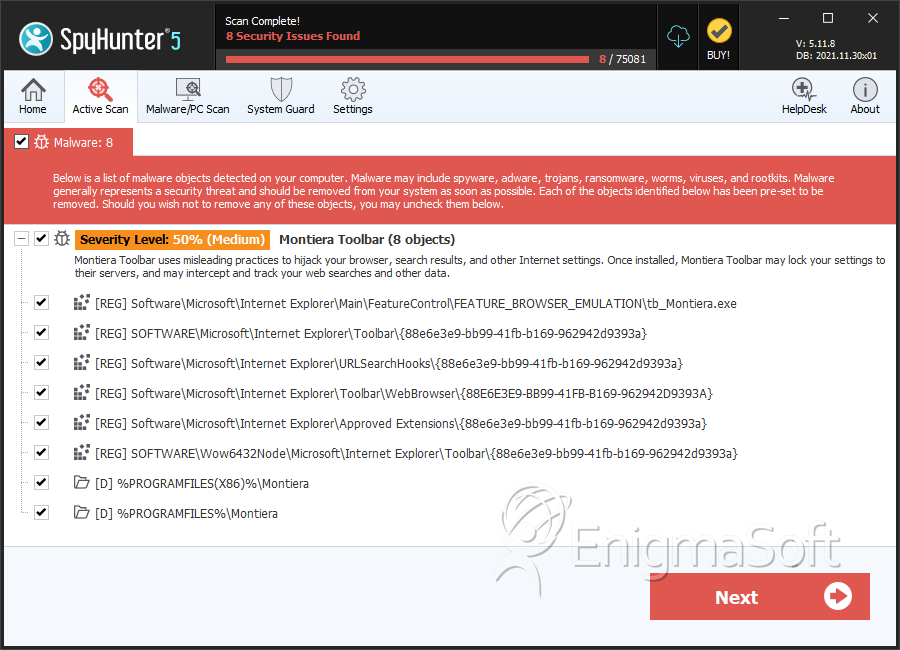
SpyHunter Detects & Remove Montiera Toolbar
Registry Details
Directories
Montiera Toolbar may create the following directory or directories:
| %APPDATA%\Montiera |
| %LOCALAPPDATA%\NativeMessaging\CT3232085 |
| %LocalAppData%\Google\Chrome\User Data\Default\Extensions\hadddalehlfhlejijophcfblmnejelkb |
| %LocalAppData%\Google\Chrome\User Data\Default\Local Extension Settings\hadddalehlfhlejijophcfblmnejelkb |
| %PROGRAMFILES%\Montiera |
| %PROGRAMFILES(X86)%\Montiera |
| %USERPROFILE%\AppData\LocalLow\Montiera |
Analysis Report
General information
| Family Name: | Montiera Toolbar |
|---|---|
| Signature status: | Self Signed |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
e7abed8be82d55a905a6a47d7c6aae18
SHA1:
e07a2e5337e7c9f7b4d861f9b8e1a2de60b6e751
SHA256:
2A016BAF99C73A3177B661CBCE2096E6D530C7B8A12649FEF759CFC9E4EAC22B
File Size:
1.30 MB, 1299822 bytes
|
|
MD5:
713498c43504a35c4477e9ff9fdb577f
SHA1:
d24573cdf723355fe830251042fcaf3369693823
SHA256:
2AF553572D152B406779547BECC7248533FD57275C4396CFFC33E1E33E580976
File Size:
1.22 MB, 1217023 bytes
|
|
MD5:
d9d8503bca3462cb405d6fe9b57a64f8
SHA1:
3649bbefd6e9d34252fa0aa6a15c953d5aa43101
SHA256:
D71387E1F3D9EFD925D0F5AF64972B2CAC7C6FC4EC25FF2B1CFAAAEEC2F8AB26
File Size:
1.22 MB, 1216977 bytes
|
|
MD5:
7c9d62e716c518261dcdb556e825fd64
SHA1:
0ba76e63633861dec0543ac872338ee0d657a849
SHA256:
41B0939B07F107D750F43BC8EC00026A6AD119706BB4CD0A047B54921B5DE151
File Size:
1.22 MB, 1217092 bytes
|
|
MD5:
98bf81c65c2c43db229e1e9f76323950
SHA1:
664229fdc87e7d0fa41ccab4479eed42143b5ac8
SHA256:
B05E5A72773AE885D9CE883722C04AD02BE3AFE82C1D6012F488413437DD57CC
File Size:
789.58 KB, 789584 bytes
|
Show More
|
MD5:
b22d54918ff4fe27be2f4e1cf2a2ebd5
SHA1:
fbd4e6e0fbba97828a8cb1e9375ba57a80a4ce9e
SHA256:
9EF88A89433E141F081507564C9AA70CFD4C00F7379E9A9829D7112A07C7C5D7
File Size:
437.32 KB, 437320 bytes
|
|
MD5:
d81c1d9ddda55a2e16ace4fe287ae76a
SHA1:
957e5a38e435a20cdbc606dc2a2f6b35456d6e4a
SHA256:
4A43B6CD198B6428554DA457AA0AF11C360FAB22E52A4F4FFDB564D85496F183
File Size:
1.22 MB, 1217073 bytes
|
|
MD5:
1a77616f52d97a842d07bce953fc6256
SHA1:
0eab122a6b3f6e8f86741c8a99966dab7dd9cb59
SHA256:
7B0227023F8B8E5B218BA0BC9E10D902E5E86061A367783D6DDA133BD0429A18
File Size:
1.22 MB, 1217084 bytes
|
|
MD5:
8e744cc9ecd11b275c099b10430b8d45
SHA1:
4d2af4a2e5937827a98e1a2aaf53f654f192e923
SHA256:
9164244B51935571997F3C7261F274F4779E4EE523B178D091A5A3E6CC42F7A7
File Size:
786.00 KB, 786000 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
Show More
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Company Name | Babylon Ltd. |
| File Description | Uninstaller Application |
| File Version |
|
| Internal Name |
|
| Legal Copyright | Copyright © Babylon Ltd. 1997-2013 |
| Original Filename |
|
| Product Name |
|
| Product Version |
|
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| Visual Tools | Thawte Code Signing CA - G2 | Hash Mismatch |
| Visual Tools | Thawte Code Signing CA - G2 | Self Signed |
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 157 |
|---|---|
| Potentially Malicious Blocks: | 2 |
| Whitelisted Blocks: | 131 |
| Unknown Blocks: | 24 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Babylon.C
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Other Suspicious |
|
| Network Info Queried |
|
| Network Wininet |
|
| Anti Debug |
|
