Lyrix Ransomware
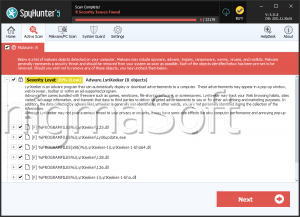
In today's technological age, protecting your devices from malware threats has become more critical than ever. With cybercriminals constantly evolving their techniques, users must be vigilant to avoid falling victim to harmful attacks, such as ransomware. One of the most sophisticated threats in recent times is the Lyrix Ransomware—a highly disruptive malware designed to lock users out of their fundamental files and request a ransom for their release. Below, we'll explore the features of this ransomware, its symptoms, and the best security practices you can adopt to safeguard your devices.
Table of Contents
What is the Lyrix Ransomware?
The Lyrix Ransomware is a particularly nasty variant of the ransomware family that encrypts all the files on an affected device, making them inaccessible to the user. The ransomware adds a unique extension consisting of ten random characters to each encrypted file, rendering it unreadable. It then leaves a README.txt file demanding payment for the decryption key.
What makes Lyrix so threatening is its stealthy distribution methods and its ability to install additional hurtful software simultaneously. In many cases, it comes bundled with password-stealing Trojans or other malware, making it even harder to recover from an infection.
How Does the Lyrix Ransomware Infect Your Device?
Lyrix typically spreads through standard malware delivery techniques. The most common distribution methods include:
- Infected Email Attachments: These attachments often contain corrupted macros that, when opened, trigger the ransomware infection.
- Torrent Websites: Downloading pirated or unsafe files from torrents is another common vector for the spread of Lyrix.
- Fraudulent Advertisements: Also known as malvertising, this method involves deceptive advertisements that, once clicked, lead to a ransomware infection.
Symptoms of a Lyrix Ransomware Infection
If your device is infected with the Lyrix Ransomware, there are a few key symptoms that you will notice immediately:
- File Extensions Change: Files that were once accessible will now have a different extension—such as .docx.locked—making them unreadable.
- Ransom Demand: A message titled README.txt will pop up on your desktop, demanding a ransom fee (usually in Bitcoin) for the decryption key.
In addition, you may find that your system performance slows down, as the ransomware can also install other types of threatening software that disrupt your device's normal functioning.
What Happens After an Infection?
Once Lyrix encrypts your files, the damage is significant. You will be unable to access any of your important files—documents, photos, and even system files. The only way to regain access to these files is to pay the ransom demanded by the attackers, which is usually in Bitcoin.
Unfortunately, there is no known free decryptor for the Lyrix Ransomware. This means that recovering encrypted files is nearly impossible without paying the ransom. Additionally, agreeing to the ransom payment does not assure that the attackers will actually provide the decryption key or refrain from targeting you again in the future.
Best Security Practices to Defend against the Lyrix Ransomware
Ransomware, especially sophisticated variants like Lyrix, can be devastating. However, there are several proactive security practices that can drastically reduce your risk of infection. Here are the top security measures you should take:
- Enable Anti-Malware Software: Keep your anti-malware software up-to-date and ensure it actively scans your system for known threats, including ransomware.
- Be Prudent with Email Attachments and Links: Never reach email attachments from unknown sources, and avoid clicking on links within suspicious emails. Many ransomware variants, including Lyrix, spread through infected email attachments containing malicious macros.
- Use a Backup System: Regularly back up your files to a secure location, preferably using an external drive or a cloud service that is not directly connected to your device. This guarantees that you can recover your important files if an infection occurs.
- Update Your Software Regularly: Always keep your operating system, software and applications upgraded. Fixes and updates often fix security vulnerabilities that ransomware like Lyrix can exploit.
- Enable Multi-Factor Authentication (MFA): For added security, use multi-factor authentication on accounts that support it, particularly email and cloud services. This makes it harder for attackers to gain unauthorized access to your accounts.
- Avoid Pirated Software and Untrustworthy Websites: Avoid downloading software from unofficial or dubious sources like torrents, which are often laced with malware.
- Use Network Segmentation: If you're operating a business or a multi-device setup, use network segmentation to limit the spread of malware between different devices. This can help contain a ransomware infection if one device is compromised.
- Train Employees on Cybersecurity: If you manage a business or a group of devices, ensure that all users are educated about the risks of phishing emails and unsafe downloads. Well-ordered training can go a long way toward preventing infections.
While the Lyrix Ransomware presents a serious threat to both individuals and businesses, adopting proactive security practices can significantly diminish the chances of falling victim to this and similar threats. By staying informed, maintaining strong security defenses, and being cautious about online activities, users can safeguard their devices against malware like Lyrix and minimize the potential damage caused by such attacks. Always remember that prevention is the best defense against ransomware.