ExpressFiles
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Popularity Rank: | 5,931 |
| Threat Level: | 10 % (Normal) |
| Infected Computers: | 46,909 |
| First Seen: | January 3, 2014 |
| Last Seen: | March 23, 2026 |
| OS(es) Affected: | Windows |
ExpressFiles is a Potentially Unwanted Program that may cause a wide variety of problems on affected computers. Potentially Unwanted Programs, usually represented using the acronym PUP, may be used by marketers to profit from advertising schemes and cause significant problems on affected computers. Software like ExpressFiles is marketed and promoted as a useful add-on for the computer user's Web browser commonly. However, in the vast majority of the cases, security researchers have observed that the many unwanted symptoms associated with these PUPs seldom warrants the supposed benefits that can be gained from using them. This happens because the prime function of these programs is to profit from advertising rather than delivering useful services to computer users.
Table of Contents
How PUPs Like ExpressFiles may be Distributed
Although PUPs may be distributed using normal threat distribution techniques (despite not being considered threats themselves), such as the use of attack websites, spam email messages or social engineering tactics, ExpressFiles and other PUPs' main form of distribution is a technique known as bundling. To do this, marketers will take programs like ExpressFiles and then bundle them with popular freeware applications, often hosted on low-quality software distribution platforms. When the computer users install these freeware programs, they may not realize that they come bundled with programs like ExpressFiles, installing the PUP on their computers in the process. Security researchers strongly advise computer users to follow the installation process carefully to prevent the entrance of any unwanted components when installing a new program on the affected computer. In almost every case, computer users may opt out of installing the PUP by selecting 'Custom' installation to detect all components being installed.
Removing ExpressFiles and Similar PUPs
PUPs like ExpressFiles may be uninstalled using normal software uninstallation methods. Once ExpressFiles has been uninstalled, however, undesirable changes to your Web browser's settings and files associated with ExpressFiles may remain. Because of this, the removal of ExpressFiles should be followed with the use of a reliable security program that is fully up-to-date and manual restoration of unwanted changes to your computer's settings may need to be done.
Aliases
14 security vendors flagged this file as malicious.
| Antivirus Vendor | Detection |
|---|---|
| Avast | Win32:Downloader-TSH [PUP] |
| AVG | Suspicion: unknown virus |
| Fortinet | W32/YourFileDownloader.B |
| Sophos | Generic PUA IA |
| McAfee-GW-Edition | Heuristic.LooksLike.Win32.SuspiciousPE.F |
| Comodo | UnclassifiedMalware |
| Avast | Win32:Dropper-gen [Drp] |
| McAfee | RDN/Generic Downloader.x!iq |
| CAT-QuickHeal | (Suspicious) - DNAScan |
| AVG | Faglaro Enterprises Limited |
| Symantec | Suspicious.Cloud |
| GData | Win32.Application.ExpressFiles.B |
| Avast | Win32:Expressfiles-C [PUP] |
| Avast | Win32:Malware-gen |
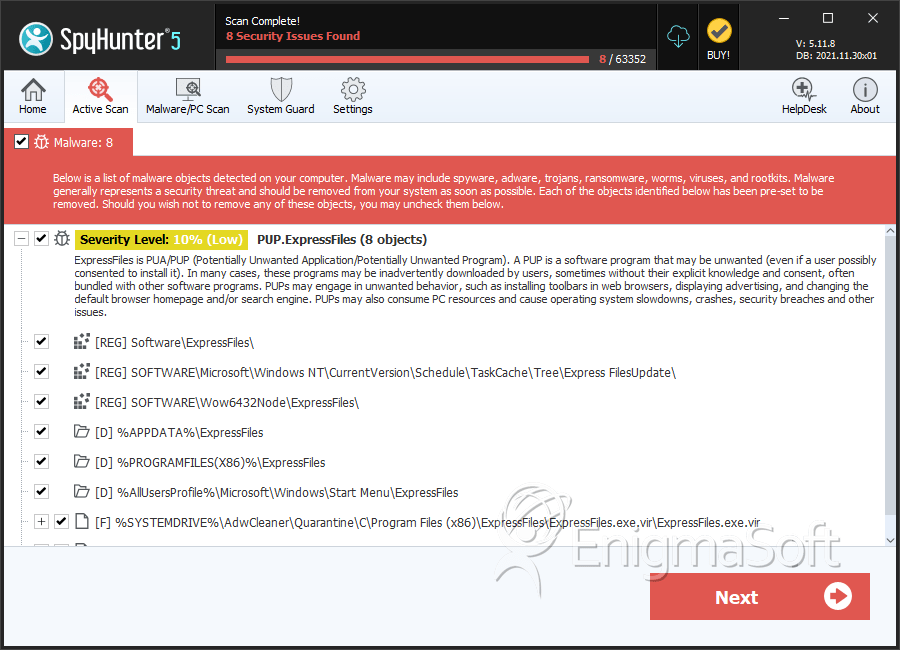
SpyHunter Detects & Remove ExpressFiles
File System Details
| # | File Name | MD5 |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|---|
| 1. | ExpressFiles.exe.vir | b4dfe0eacb9316f302334b6b646f48bc | 1,215 |
| 2. | $RZ8MZOC.exe | 0dd2d9d2719b7d9c332cfa28eaf9d3dd | 1,142 |
| 3. | uninstall464929.exe | 76f6e8033be7099c2d26b130f336bc7d | 1,041 |
| 4. | EFupdater.exe1 | 36f420e4b802bcd0243bc8d7f231136d | 1,028 |
| 5. | ExpressFiles.exe | 0094df60653a6183ac40b620c3d244e8 | 656 |
| 6. | expressdl.exe.vir | 5160c77602fc9ee2494b8c4a6ca7b02a | 90 |
| 7. | uninstall83772318.exe | 708ede8d0a6353bebd6a7609fa594d4c | 86 |
| 8. | EFupdater.exe | 88ea4ba7ad5dcd53e297433da6e388d8 | 40 |
| 9. | uninstall1302328.exe | f695008e91430af040cad5173e423d63 | 36 |
Registry Details
Directories
ExpressFiles may create the following directory or directories:
| %APPDATA%\ExpressFiles |
| %AllUsersProfile%\Microsoft\Windows\Start Menu\ExpressFiles |
| %PROGRAMFILES%\ExpressFiles |
| %PROGRAMFILES(X86)%\ExpressFiles |
Analysis Report
General information
| Family Name: | PUP.ExpressFiles |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
00aa28473fe353c8861dd5d227523d34
SHA1:
efdf719917c2130834db79fd69811eff8846e83f
SHA256:
E417681B74865743762C9DEBB204321F4F59A21C90B5398345DD9A167A764F9F
File Size:
3.47 MB, 3467928 bytes
|
|
MD5:
92866f0155754849e49e0aec7c193be3
SHA1:
55b96afd5201733f9ce3a50afdd1b680df9fe520
SHA256:
DC3BFDDBC30481E6F1BD9363D0B25793EDB5F9033AF91E82D0CE9E5467663845
File Size:
3.37 MB, 3372093 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have exports table
- File doesn't have relocations information
- File doesn't have security information
- File has exports table
- File has TLS information
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
Show More
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
File Icons
File Icons
This section displays icon resources found within family samples. Malware often replicates icons commonly associated with legitimate software to mislead users into believing the malware is safe.Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Comments | This installation was built with Inno Setup. |
| Company Name |
|
| File Description |
|
| File Version |
|
| Internal Name | Installer |
| Legal Copyright | Copyright (C) 2015 |
| Original Filename | Installer.exe |
| Product Name |
|
| Product Version |
|
Digital Signatures
Digital Signatures
This section lists digital signatures that are attached to samples within this family. When analyzing and verifying digital signatures, it is important to confirm that the signature’s root authority is a well-known and trustworthy entity and that the status of the signature is good. Malware is often signed with non-trustworthy “Self Signed” digital signatures (which can be easily created by a malware author with no verification). Malware may also be signed by legitimate signatures that have an invalid status, and by signatures from questionable root authorities with fake or misleading “Signer” names.| Signer | Root | Status |
|---|---|---|
| Ignore Idea LLC | Ignore Idea LLC | Self Signed |
File Traits
- 2+ executable sections
- HighEntropy
- Inno
- InnoSetup Installer
- Installer Manifest
- Installer Version
- VirtualQueryEx
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 7,525 |
|---|---|
| Potentially Malicious Blocks: | 0 |
| Whitelisted Blocks: | 7,525 |
| Unknown Blocks: | 0 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Banker.LH
- Banker.R
- Ousaban.V
Files Modified
Files Modified
This section lists files that were created, modified, moved and/or deleted by samples in this family. File system activity can provide valuable insight into how malware functions on the operating system.| File | Attributes |
|---|---|
| c:\users\user\appdata\local\temp\fr4zvi1q3d.tmp\htmlayout.dll | Generic Write,Read Attributes |
Registry Modifications
Registry Modifications
This section lists registry keys and values that were created, modified and/or deleted by samples in this family. Windows Registry activity can provide valuable insight into malware functionality. Additionally, malware often creates registry values to allow itself to automatically start and indefinitely persist after an initial infection has compromised the system.| Key::Value | Data | API Name |
|---|---|---|
| HKLM\software\microsoft\windows nt\currentversion\notifications\data::418a073aa3bc1c75 | RegNtPreCreateKey |
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Anti Debug |
|
| User Data Access |
|