Error Doctor 2009
Threat Scorecard
EnigmaSoft Threat Scorecard
EnigmaSoft Threat Scorecards are assessment reports for different malware threats which have been collected and analyzed by our research team. EnigmaSoft Threat Scorecards evaluate and rank threats using several metrics including real-world and potential risk factors, trends, frequency, prevalence, and persistence. EnigmaSoft Threat Scorecards are updated regularly based on our research data and metrics and are useful for a wide range of computer users, from end users seeking solutions to remove malware from their systems to security experts analyzing threats.
EnigmaSoft Threat Scorecards display a variety of useful information, including:
Popularity Rank: The ranking of a particular threat in EnigmaSoft’s Threat Database.
Severity Level: The determined severity level of an object, represented numerically, based on our risk modeling process and research, as explained in our Threat Assessment Criteria.
Infected Computers: The number of confirmed and suspected cases of a particular threat detected on infected computers as reported by SpyHunter.
See also Threat Assessment Criteria.
| Threat Level: | 20 % (Normal) |
| Infected Computers: | 3 |
| First Seen: | November 28, 2011 |
| Last Seen: | February 16, 2026 |
| OS(es) Affected: | Windows |

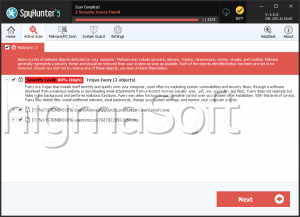
Error Doctor 2009 Image
Despite its name, Error Doctor 2009 is not designed to fix errors on your computer system or to help your operating system in any way. Rather, Error Doctor 2009 is part of a fairly widespread online scam, designed to steal your money by convincing you to purchase a useless fake anti-spyware application. According to ESG security researchers, there is nothing remotely associated with a legitimate anti-spyware program beyond Error Doctor 2009's interface. While on the surface, Error Doctor 2009 is designed to resemble legitimate security programs, Error Doctor 2009 is designed for nothing more than to display a large number of fake error messages and alerts in order to convince its victim to purchase a useless 'full version' of Error Doctor 2009. ESG security researchers recommend removing Error Doctor 2009 with a legitimate security program. Because Error Doctor 2009 may be able to block access to the Internet or to your real security applications, it may be necessary to start up Windows in Safe Mode. This will allow you to bypass Error Doctor 2009's host of error messages and malicious actions long enough to download and install a real security solution.
Table of Contents
Protecting Yourself from Error Doctor 2009
Error Doctor 2009 will usually be installed through a Trojan infection. Once installed, this Trojan will download and install Error Doctor 2009's components and make harmful changes to your computer system. Once Error Doctor 2009 is up and running, Error Doctor 2009 launches automatically every time you start up your operating system, taking over your computer system, unless you decide to remove Error Doctor 2009. Some ways in which Trojans associated with Error Doctor 2009 can make their way onto your computer include the following:
- Trojans associated with security programs such as Error Doctor 2009 will often be acquired after clicking on a pop-up window resembling an error message, claiming that your computer system is infected with malware. Pop-up windows and advertisements claiming to run a full malware scan of your computer or to give you your PC's rating are usually associated with rogue security programs and dangerous Trojans.
- It is also fairly common to find Trojans associated with Error Doctor 2009 disguised as fake system updates, video codecs or popular files on file sharing networks.
- Error Doctor 2009's associated malware and installer may also be included within a suspicious email attachment or through other spam messaging scams.
File System Details
| # | File Name |
Detections
Detections: The number of confirmed and suspected cases of a particular threat detected on
infected computers as reported by SpyHunter.
|
|---|---|---|
| 1. | %Common Program Files%\InstallShield\Professional\RunTime\11\00\Intel32\ctor.dll | |
| 2. | %Common Program Files%\InstallShield\Professional\RunTime\Objectps.dll | |
| 3. | %Common Program Files%\InstallShield\Professional\RunTime\11\00\Intel32\iscript.dll | |
| 4. | %Common Program Files%\InstallShield\Professional\RunTime\11\00\Intel32\DotNetInstaller.exe | |
| 5. | %Common Program Files%\InstallShield\Professional\RunTime\11\00\Intel32\iuser.dll | |
| 6. | %Common Program Files%\InstallShield\Professional\RunTime\11\00\Intel32\iKernel.dll | |
| 7. | ErrorDoctor.exe | |
| 8. | %Program Files%\SoftwareDoctor\ErrorDoctor\ErrorDoctor.exe | |
| 9. | %Common Program Files%\InstallShield\Professional\RunTime\11\00\Intel32\iGdi.dll | |
| 10. | %Common Program Files%\InstallShield\Professional\RunTime\11\00\Intel32\setup.dll | |
| 11. | DotNetInstaller.exe | |
| 12. | %Program Files%\SoftwareDoctor\ErrorDoctor\icon.ico | |
| 13. | %Documents and Settings%\All Users\Start Menu\Programs\SoftwareDoctor\ErrorDoctor\Uninstall.lnk | |
| 14. | %Documents and Settings%\All Users\Start Menu\Programs\SoftwareDoctor\ErrorDoctor\ErrorDoctor.lnk | |
| 15. | %Common Program Files%\InstallShield\Professional\RunTime\IsProBE.tlb | |
| 16. | %Documents and Settings%\All Users\Desktop\ErrorDoctor.lnk | |
| 17. | %Common Program Files%\InstallShield\Professional\RunTime\iKernel.rgs |
Registry Details
Analysis Report
General information
| Family Name: | Adware.Cydoor.A |
|---|---|
| Signature status: | No Signature |
Known Samples
Known Samples
This section lists other file samples believed to be associated with this family.|
MD5:
2460e08c02b3b63f3b32f152d3610d17
SHA1:
47fc85546f3b09b917c4afedb2bad8e06d642ac1
SHA256:
35F0F4E8EA80140FC10412BFF5F6B6CD4DE0331555E72DDD8ABEF1BD4326E1C1
File Size:
237.57 KB, 237568 bytes
|
Windows Portable Executable Attributes
- File doesn't have "Rich" header
- File doesn't have debug information
- File doesn't have security information
- File has exports table
- File is 32-bit executable
- File is either console or GUI application
- File is GUI application (IMAGE_SUBSYSTEM_WINDOWS_GUI)
- File is Native application (NOT .NET application)
- File is not packed
- IMAGE_FILE_DLL is not set inside PE header (Executable)
Show More
- IMAGE_FILE_EXECUTABLE_IMAGE is set inside PE header (Executable Image)
Windows PE Version Information
Windows PE Version Information
This section displays values and attributes that have been set in the Windows file version information data structure for samples within this family. To mislead users, malware actors often add fake version information mimicking legitimate software.| Name | Value |
|---|---|
| Comments | This is a module of Cydoor's ad system. Additional information is available at http://www.cydoor.com |
| Company Name | Cydoor Technologies, Inc. |
| File Description | Cydoor Techonologies ad-system |
| File Version | 2, 0, 4, 5 |
| Internal Name | CD_Clint.dll |
| Legal Copyright | Copyright (C) Cydoor Technologies, Inc. 1999-2000 |
| Legal Trademarks | Cydoor Technologies(tm) |
| Original Filename | CD_Clint.dll |
| Product Name | Cydoor Techonologies ad-system |
| Product Version | 2, 0, 4, 5 |
| Special Build | 1 |
File Traits
- dll
- HighEntropy
- x86
Block Information
Block Information
During analysis, EnigmaSoft breaks file samples into logical blocks for classification and comparison with other samples. Blocks can be used to generate malware detection rules and to group file samples into families based on shared source code, functionality and other distinguishing attributes and characteristics. This section lists a summary of this block data, as well as its classification by EnigmaSoft. A visual representation of the block data is also displayed, where available.| Total Blocks: | 795 |
|---|---|
| Potentially Malicious Blocks: | 347 |
| Whitelisted Blocks: | 448 |
| Unknown Blocks: | 0 |
Visual Map
? - Unknown Block
x - Potentially Malicious Block
Similar Families
Similar Families
This section lists other families that share similarities with this family, based on EnigmaSoft’s analysis. Many malware families are created from the same malware toolkits and use the same packing and encryption techniques but uniquely extend functionality. Similar families may also share source code, attributes, icons, subcomponents, compromised and/or invalid digital signatures, and network characteristics. Researchers leverage these similarities to rapidly and effectively triage file samples and extend malware detection rules.- Cydoor.A
Windows API Usage
Windows API Usage
This section lists Windows API calls that are used by the samples in this family. Windows API usage analysis is a valuable tool that can help identify malicious activity, such as keylogging, security privilege escalation, data encryption, data exfiltration, interference with antivirus software, and network request manipulation.| Category | API |
|---|---|
| Syscall Use |
Show More
|
| Process Manipulation Evasion |
|
| Process Shell Execute |
|
| Anti Debug |
|
Shell Command Execution
Shell Command Execution
This section lists Windows shell commands that are run by the samples in this family. Windows Shell commands are often leveraged by malware for nefarious purposes and can be used to elevate security privileges, download and launch other malware, exploit vulnerabilities, collect and exfiltrate data, and hide malicious activity.
C:\WINDOWS\SysWOW64\rundll32.exe C:\WINDOWS\system32\rundll32.exe c:\users\user\downloads\47fc85546f3b09b917c4afedb2bad8e06d642ac1_0000237568.,LiQMAxHB
|