Cowa Ransomware
As digital threats continue to evolve in sophistication and scale, staying informed and vigilant is more critical than ever. Among the many dangerous strains of ransomware currently circulating, Cowa Ransomware stands out as a particularly insidious variant. Belonging to the notorious Makop ransomware family, Cowa is designed to encrypt victims' data, extort ransom payments, and instill fear through threats of data theft and exposure. This analysis explores how Cowa operates, the damage it can cause, and most importantly, how users can defend against such threats.
Table of Contents
Encryption with a Menacing Signature
Once Cowa Ransomware infects a device, it begins encrypting a wide range of file types, rendering them unusable. What sets this strain apart is how it alters the filenames of affected data. Each encrypted file is renamed to include a victim-specific ID, the attacker's contact email, and the '.cowa' extension. For example, a simple image file like '1.png' may become '1.png.[2AF20FA3].[suppcowa@outlook.com].cowa.'
After the encryption process completes, the malware replaces the system's desktop wallpaper and drops a ransom note titled '+README-WARNING+.txt.' This message is a carefully crafted threat, notifying the victim that their files have been both encrypted and allegedly stolen. The note claims that unless the victim contacts the attackers, their data will remain locked, and potentially leaked publicly.
Victims are urged to email the cybercriminals at 'suppcowa@outlook.com' to begin the ransom negotiation process. Additionally, the note warns against attempting file recovery without assistance, as unauthorized efforts could make decryption impossible.
No Guarantees: The Dangers of Paying the Ransom
Cowa, like most ransomware, employs strong encryption algorithms that are virtually impossible to break without access to the attackers' private decryption key. While victims may feel pressured to pay the ransom, doing so is extremely risky. Cybercriminals are under no obligation to fulfill their promises, and many victims report never receiving decryption tools even after payment.
Furthermore, paying the ransom funds criminal operations and encourages the continued development of malicious software. It also signals to attackers that a particular victim, or organization, is willing to comply, increasing the risk of future attacks.
Because of this, cybersecurity professionals universally recommend against paying ransoms. Instead, users should focus on containment, removal, and data recovery through legitimate means, such as restoring from secure backups.
How Cowa Finds Its Way In
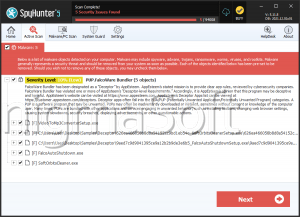
The methods used to distribute Cowa Ransomware are varied and highly deceptive. Threat actors often rely on phishing emails, fake software downloads, and malicious online ads to trick users into downloading the malware. These malicious payloads are typically disguised as seemingly harmless file types, such as Microsoft Office documents, PDFs, ZIP or RAR archives, JavaScript files, or executable programs.
More advanced techniques involve the use of backdoor trojans, drive-by downloads from compromised websites, or bundled software installers from shady third-party sources. Attackers also exploit vulnerabilities in outdated software to silently install ransomware in the background. Additionally, some variants may propagate across local networks or through infected USB devices, allowing the malware to spread from system to system.
Fortifying Your Digital Defenses: Best Practices for Ransomware Protection
Preventing ransomware like Cowa from taking hold requires a strong and consistent cybersecurity posture. Users and organizations must combine technical safeguards with informed user behavior. Key recommendations to minimize the risk of infection include:
- Always keep operating systems, software, and security tools up to date. Vulnerabilities in outdated programs are often exploited by attackers.
- Use a reputable and up-to-date anti-malware solution that includes real-time protection and heuristic scanning.
- Disable macros and active content in Office documents unless they are from trusted sources.
Final Thoughts: Vigilance Is the Best Defense
Cowa Ransomware is a potent example of how far cybercriminals are willing to go to extort victims and capitalize on their panic. As a part of the Makop family, it carries the hallmark traits of a well-developed and highly destructive malware strain. However, through proactive cybersecurity measures, careful user behavior, and regular data backups, the risk of falling victim to ransomware can be significantly reduced. In the ever-evolving landscape of cyber threats, preparation and awareness are the most reliable shields.